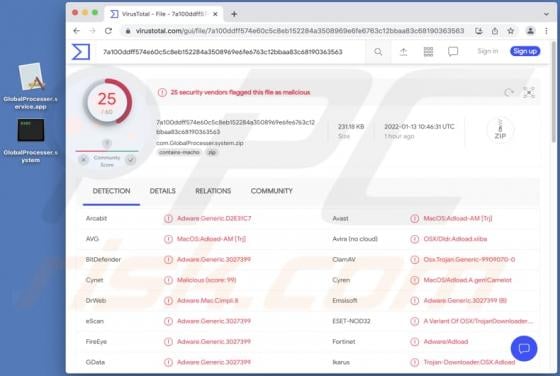
DigitalProgram Adware (Mac)
Our researchers have found yet another adware-type application called DigitalProgram. We have concluded that this piece of software operates as adware. It also belongs to the AdLoad malware family. We have researched many samples from said group, and while during our testing - we did not observ