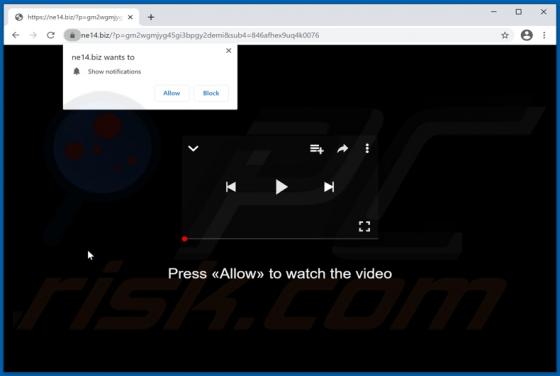
Ne.biz Ads
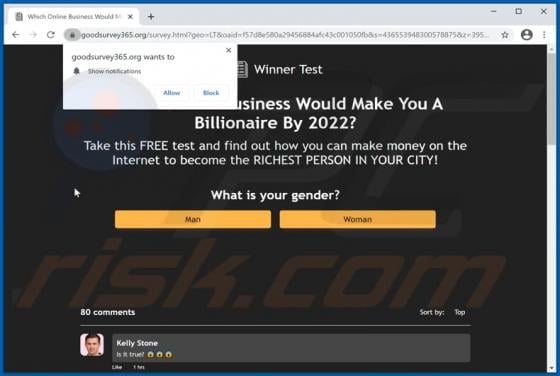
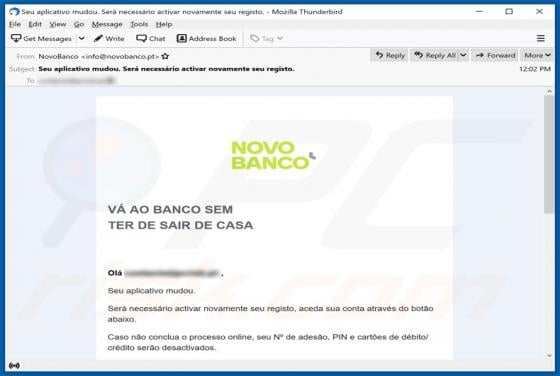
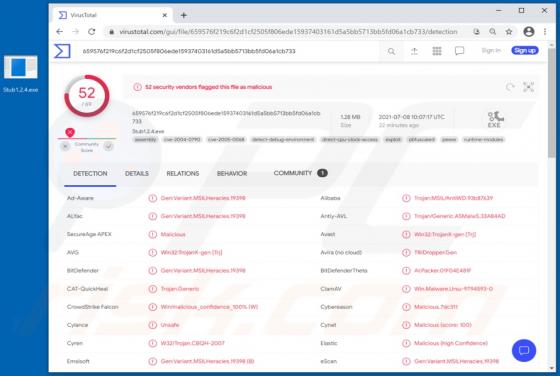
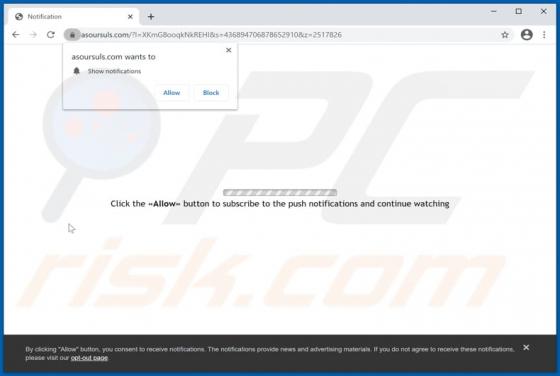
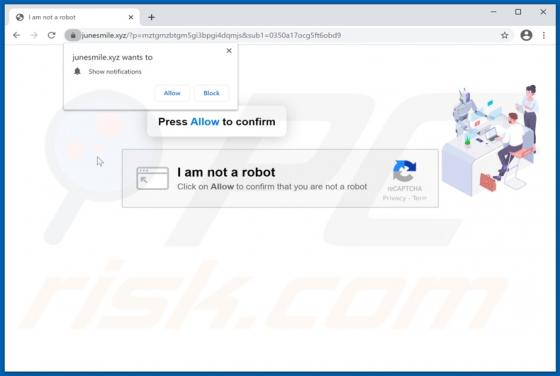
Ne[.]biz (and this domain's variations, e.g., ne03[.]biz, ne06[.]biz, ne10[.]biz, ne11[.]biz, ne14[.]biz, ne17[.]biz, etc.) is a rogue website. It is designed to load dubious content and/or redirect visitors to other sites (likely untrustworthy and malicious ones). The Internet is rife with such