Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What is System Restore?
System Restore is fake computer scanner that attempts to trick PC users into purchasing a fake license. This bogus program is derived from the same family of misleading applications as Data Repair, Data Restore, and many others.
Like its predecessors, the creators of System Restore attempt to convince computer users that their systems have serious hardware problems that could lead to severe data loss. This rogue scanner is distributed through misleading websites that exploit various security vulnerabilities in order to install these fake computer programs.
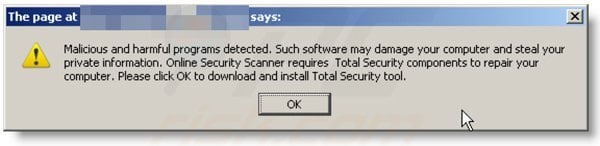
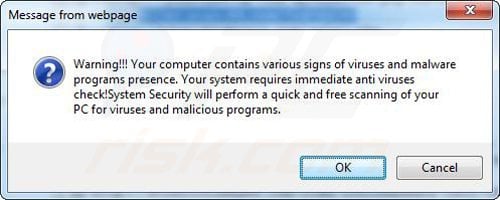
When infected with System Restore, you will notice a system scan being performed each time you boot your operating system. System Restore will also display various warning pop-up messages reporting computer hardware malfunctions, computer RAM errors, or hard drive bad sectors.
This bogus program will also hide your desktop icons and start menu items.

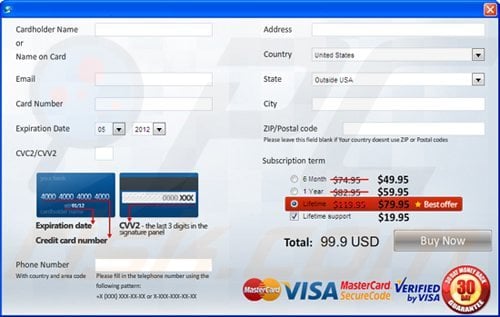
If you click the 'Fix Errors' button in the main window of this program, you will be redirected to a website where you will be asked to purchase a full version of System Restore in order to remove the 'detected' system errors. Do not buy this program, it is a scam.
The scans are performed to scare you into believing that you may lose your stored data. Ignore these fake warning messages, since System Restore does not actually scan your computer, this process is merely imitated.
Your desktop icons and other information is not lost; System Restore simply hides it, and by using this removal guide, you can completely remove System Restore and regain control of your hidden files. This malicious program 'detects' non-existent hard drive errors to scare you into believing that you could potentially suffer data loss.
Today, computer users store very important data on their hard drives, thus creators of this rogue program use this to their advantage by promoting this misleading strategy to scare PC users. Therefore, do not trust this software and eliminate it from your PC immediately.
System Restore bogus program will display the following fake pop-up messages:
"Critical Error. Hard drive clusters are partly damaged. Segment load failure."
"System Error. An error occurred while reading system files. Run a system diagnostic utility to check your hard disk drive for errors."
"Critical Error. RAM memory usage is critically high. RAM memory failure."
"Critical Error. Windows cannot find hard disk space. Hard drive error."
"Activation Reminder. System Restore Activation. Advanced module activation required to fix detected errors and performance issues. Please purchase Advanced Module license to activate this software and enable all features."
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is System Restore?
- STEP 1. Remove System Restore using a registration key.
- STEP 2. Remove System Restore using Safe Mode with Networking.
- STEP 3. Remove System Restore manually by deleting files and registry entries.
- STEP 3. Restore hidden files and icons.
Automatic System Restore spyware removal:
Step 1
Download and scan your computer with Kaspersky's TDSS Killer. Download TDSS Killer. (System Restore infects your computer along with a rootkit infection. For smooth removal, you need to remove this rootkit infection first).
Step 2
Before downloading the spyware remover, enter the System Restore registration key in the registration window. Click "Click here to activate full-functional version" located on the bottom-left of the main window and enter this key:
E-mail: fake(at)email.com Key: 1203978628012489708290478989147
When the registration key is entered, System Restore will behave as if you have purchased it and will stop generating fake warnings. It will also enable some previously disabled Windows features.
Note that registering this program will not remove it from your PC. It will simply disable the fake warnings and enable you to install the spyware remover.
After you enter this key, you can download Remover (use the button below) and remove this fake security software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Manual Step-by-step removal instructions of System Restore.
If you are unable to remove System Restore, you can use these manual removal instructions. Use them at your own risk, since if you do not have strong computer knowledge, you could harm your operating system.
Use them only if you are an experienced computer user. (Instructions on how to end processes, remove registry entries...)
E-mail: fake(at)email.com
Key: 1203978628012489708290478989147
If this works, the bogus program will be disabled and you will be able to remove it without continual interventions. Note that this infection constantly mutates, and thus keys may be changed.
After this procedure, you will be able to see your files and install a legitimate spyware remover to remove this infection. If the registration key does not work, proceed to Step 2.
Warning! Entering the activation key will not remove this infection! It will simply disable the fake warnings. This spyware will run in the background and continue collecting your data!
Step 2
Start your computer in Safe Mode. Click Start, click Shut Down, click Restart, click OK.
During your computer starting process press the F8 key on your keyboard multiple times until you see the Windows Advanced Option menu, then select Safe Mode with Networking from the list.{jcomments on}

Here is a video demonstrating how to start Windows in "Safe Mode with Networking":
Windows XP users:
Windows Vista / 7 users:
Windows 8 users:
Step 3
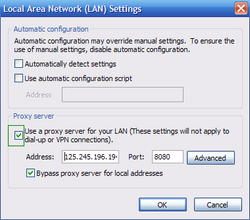
Open Internet Explorer, click Tools and select Internet Options. Select "Connections".


Step 4
Click LAN settings, if 'Use a proxy server for your LAN' is checked, uncheck it and press OK.

Step 5
Download HijackThis and save it to your desktop. Some malicious programs are able to block HijackThis, so when you click the download link, in the Save dialog, rename HijackThis.exe to iexplore.exe and only then click the Save button.
After saving the file to your desktop, double click it. In the main HijackThis window click the “Do a system scan only” button. Select the following entries (place a tick at the left of the entries):
O4 - HKCU\..\Run: [.exe] %LocalAppData%\.exe
O4 - HKCU\..\Run: [] %LocalAppData%\.exe
After selecting the required entries, click "Fix Checked". After this procedure you can close HijackThis and proceed to the next removal step.
Perform these actions:
End this System Restore process:
[random.exe]
Remove these System Restore registry entries:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer "NoDesktop" = '1'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System "DisableTaskMgr" = '1'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ".exe"
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run ""
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\system "DisableTaskMgr" = '1'
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download "CheckExeSignatures" = 'no'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced "Hidden" = '0'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced "ShowSuperHidden" = '0'
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main "Use FormSuggest" = 'Yes'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "CertificateRevocation" = '0'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "WarnonBadCertRecving" = '0'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\ActiveDesktop "NoChangingWallPaper" = '1'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations "LowRiskFileTypes" = '/{hq:/s`s:/ogn:/uyu:/dyd:/c`u:/bnl:/ble:/sdf:/lrh:/iul:/iulm:/fhg:/clq:/kqf:/`wh:/lqf:/lqdf:/lnw:/lq2:/l2t:/v`w:/rbs:'
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments "SaveZoneInformation" = '1'
Delete these System Restore files:
%Temp%\smtmp\
%Temp%\smtmp\1
%Temp%\smtmp\1
%Temp%\smtmp\2
%Temp%\smtmp\3
%Temp%\smtmp\4
%LocalAppData%\
%LocalAppData%\.exe
%LocalAppData%\~
%LocalAppData%\~
%StartMenu%\Programs\System Restore
%StartMenu%\Programs\System Restore\System Restore.lnk
%StartMenu%\Programs\System Restore\Uninstall System Restore.lnk
Step 6
Download and install anti-spyware software to completely remove the infection.
Complete these steps if, after removal of System Restore spyware, your Desktop icons or files are hidden:
Step 1
This Infection Hides most user files. If you cannot see your files, do not panic. The files are not missing, they are simply hidden.
When downloaded, spyware remover removes the infection. Please download and run this tool to unhide your files (link below).
It is important to run this tool only when the infection has been removed from your computer. This 'unhide files' tool will be useless if you run it on an infected computer.
When the 'unhide files' tool finishes, your Windows desktop icons may remain hidden. To fix missing desktop items after spyware infection, download this .REG file.
Double click when downloaded, click Yes, and then click OK. Reboot your computer and your desktop items should now be visible.
Step 2
Reboot your computer to check if everything is OK and that the System Restore rogue spyware has been eliminated. Check to see if you can find all of your files. If some files are remain missing, open My Computer, click Tools, then select Folder Options... and under the View tab, select the radio button 'Show hidden files and folders', press OK.
You should now see all hidden files and folders. To unhide them, right click on the file or folder, then select Properties, and uncheck the 'Hidden' Check box.
That's it! You're done.
After removal completes, perform these steps to 'unhide' files and desktop icons.
Summary:
The fake antivirus programs (also known as "rogue antivirus programs" or "scareware") are applications that tries to lure computer users into paying for their non-existent full versions to remove the supposedly detected security infections (although the computer is actually clean). These bogus programs are created by cyber criminals who design them to look as legitimate antivirus software. Most commonly rogue antivirus programs infiltrate user's computer using poop-up windows or alerts which appear when users surf the Internet. These deceptive messages trick users into downloading a rogue antivirus program on their computers. Other known tactics used to spread scareware include exploit kits, infected email messages, online ad networks, drive-by downloads, or even direct calls to user's offering free support.
A computer that is infected with a fake antivirus program might also have other malware installed on it as rogue antivirus programs often are bundled with Trojans and exploit kits. Noteworthy that additional malware that infiltrates user's operating system remains on victim's computer regardless of whether a payment for a non-existent full version of a fake antivirus program is made. Here are some examples of fake security warning messages that are used in fake antivirus distribution:
Computer users who are dealing with a rogue security software shouldn't buy it's full version. By paying for a license key of a fake antivirus program users would send their money and banking information to cyber criminals. Users who have already entered their credit card number (or other sensitive information) when asked by such bogus software should inform their credit card company that they have been tricked into buying a rogue security software. Screenshot of a web page used to lure computer users into paying for a non-existent full version of system restore rogue and other rogue antivirus programs:
To protect your computer from system restore rogue and other rogue antivirus programs users should:
- Keep their operating system and all of the installed programs up-to-date.
- Use legitimate antivirus and anti-spyware programs.
- Use caution when clicking on links in social networking websites and email messages.
- Don't trust online pop-up messages which state that your computer is infected and offers you to download security software.
Symptoms indicating that your operating system is infected with a fake antivirus program:
- Intrusive security warning pop-up messages.
- Alerts asking to upgrade to a paid version of a program to remove the supposedly detected malware.
- Slow computer performance.
- Disabled Windows updates.
- Blocked Task Manager.
- Blocked Internet browsers or inability to visit legitimate antivirus vendor websites.
If you have additional information on system restore rogue or it's removal please share your knowledge in the comments section below.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion