Avoid getting scammed by fake "I Compromised Your Operating System" emails
Phishing/ScamAlso Known As: "I Compromised Your Operating System" sextortion scam
Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of email is "I Compromised Your Operating System"?
After reviewing the "I Compromised Your Operating System" email, we determined that it is spam. The letter falsely claims that the sender has infected the recipient's devices with a trojan. This malware was used to record and edit a compromising video of the recipient, which will be leaked to their contacts unless the sender is paid. This email is a sextortion scam, and as such – all the information provided by it is false.

"I Compromised Your Operating System" email scam overview
This scam email states that the recipient's operating system was compromised by the sender. The undetectable trojan-type malware was used to extract private information from all of the recipient's devices, including contact lists, email and social media accounts, messengers, chats, etc.
Furthermore, the sender alleges to have utilized the infected device's camera to record the user when they were visiting websites that host pornographic content. The footage was spliced into a video showing the recipient and the content they were viewing.
Unless the sender is paid 1300 USD in Bitcoin cryptocurrency, this sexually explicit video will be sent to all their contacts, and their personal information will be leaked online. The recipient is given three days to comply with these ransom demands. They are warned against seeking aid from the authorities, as should they do so – the sender will make good on their threats.
As mentioned in the introduction, all the claims made by the "I Compromised Your Operating System" email are false. This means that neither are the recipient's devices infected with the alleged malware nor is the sender in possession of the compromising content they claim to have.
This mail is a scam, and all of its threats are empty. By trusting this email, the victim will experience a financial loss. What is more, due to the practically untraceable nature of cryptocurrency transactions – they cannot be reversed, and victims will be unable to retrieve their funds.
| Name | "I Compromised Your Operating System" sextortion scam |
| Threat Type | Phishing, Scam, Social Engineering, Fraud |
| Fake Claim | Recipient's devices were infected and used to record compromising videos, which will be leaked to their contacts unless the sender is paid. |
| Cyber Criminal Cryptowallet Addresses | 112b2rLHpqs6fjmpvxmEEghhDWTY6HL1v3, 1JhZd6jfvfwJahTTLSsRpUh6o53qCmajL |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Monetary loss |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Sextortion spam campaign examples
"Operating System Was Compromised Under My Direction", "Hello My Perverted Friend", and "This Email Concerns Your Information Security" are just a few of our latest articles on sextortion spam campaigns. While the end goal of spam mail is to generate revenue, how that is achieved differs.
The most common uses of these emails include tricking recipients into transferring funds to scammers, revealing sensitive information (e.g., log-in credentials, personally identifiable details, credit card numbers, etc.), and downloading/installing malware.
While spam emails are infamous for being riddled with errors, they may be competently crafted and even believably disguised as messages from legitimate companies, organizations, service providers, authorities, and other entities.
How do spam campaigns infect computers?
Cyber criminals often use spam campaigns to proliferate malware. Deceptive emails/messages can include malicious files as attachments or download links. These files come in various formats, e.g., documents (PDF, Microsoft Office, Microsoft OneNote, etc.), archives (RAR, ZIP, etc.), executables (.exe, .run, etc.), JavaScript, and so forth.
Once an infectious file is opened – the malware download/installation chain is initiated. Some formats can require additional actions to jumpstart these processes. For example, Microsoft Office files need users to enable macro commands (i.e., editing/content), while OneNote documents require them to click on embedded files/links.
How to avoid installation of malware?
We recommend caution with incoming emails, PMs/DMs, SMSes, and other messages. Attachments or links present in suspicious mail must not be opened, as they can be virulent. Another recommendation is to use Microsoft Office versions released after 2010 since their "Protective View" mode prevents automatic macro execution.
However, malware is not distributed only via spam mail. Therefore, we also advise being careful while browsing, as fraudulent and malicious online content typically appears genuine and innocuous.
Furthermore, all downloads must be made from official and verified channels. It is important to activate and update software using legitimate functions/tools, as illegal activation tools ("cracks") and third-party updaters may contain malware.
We must emphasize that having a dependable anti-virus installed and kept updated is essential to device/user safety. Security programs must be used to run regular system scans and to remove detected threats and issues. If you've already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
Text presented in the "I Compromised Your Operating System" spam email letter:
Subject: Re:
Hey There.
The following is your very last notification.
I compromised your operating system thru the Wifi modem you were connecting to.
Several weeks prior, I entered the systems that you previously used to get on-line.
All the info from your electronics and devices has been immediately duplicated to my hosting space.
I can take advantage of all your cellphone messengers, social media sites, emails, chats, & list of contacts.
My trojan regularly changes its signature (driver-type), for that reason it remains not visible to anti-virus software.
I suppose now you understand, the reasons why I remained unseen until this current day
Whilst get together infos about yourself, I discovered that you are a big fan of porno sites and much more.
You really love to visit mature web pages and view kinky videos whilst getting an orgasm.
I have surely created a cam recording of you jacking off.
The cropping and editing of the videos you were seeing at the same time and your masturbation.
Your own facial expression is clearly seeable. I don't believe this sort of information will be good for your personal status.
I can direct this video footage out to everybody who know who you are.
I also have no trouble with making all your confidential information open public on the net.
I do believe you know what I mean.
It may be an absolute frustration for you personally.
I can wreck your life forever.
I suspect that you seriously don't want this to occur.
Let us fix it this way: you transfer me 1300 $ (usd) using btc equivalent at the moment of exchange), and i'll promptly get rid of all of your data from my machines.
Proceeding that, we'll forget about one another.
My bitcoin wallet address for transfering: 112b2rLHpqs6fjmpvxmEEghhDWTY6HL1v3
If you do not realize how to transmit money and what exactly btc is. Then key in the Google "Get btc".
I give you 3 days to send the funds.
The time launched counting automatically after you opened this e
mail.
I will see a message when this email is exposed.
Do not try and search for help, as the wallet address cannot be monitored, e-mail the letter is coming from & cannot be followed either & generated automatically, so there is no reason for messaging me.
Don't try to get hold of the police and other security services, & should you choose to do, your own information will undoubtedly be posted.
Changing passwords online in social network sites, e mail, & devices will not help you, since all the info is already downloaded to my servers.
Good luck and try to not do something foolish. Think of your possible future.
Appearance of the "I Compromised Your Operating System" spam email (GIF):

A Lithuanian variant of "I Compromised Your Operating System" spam email:
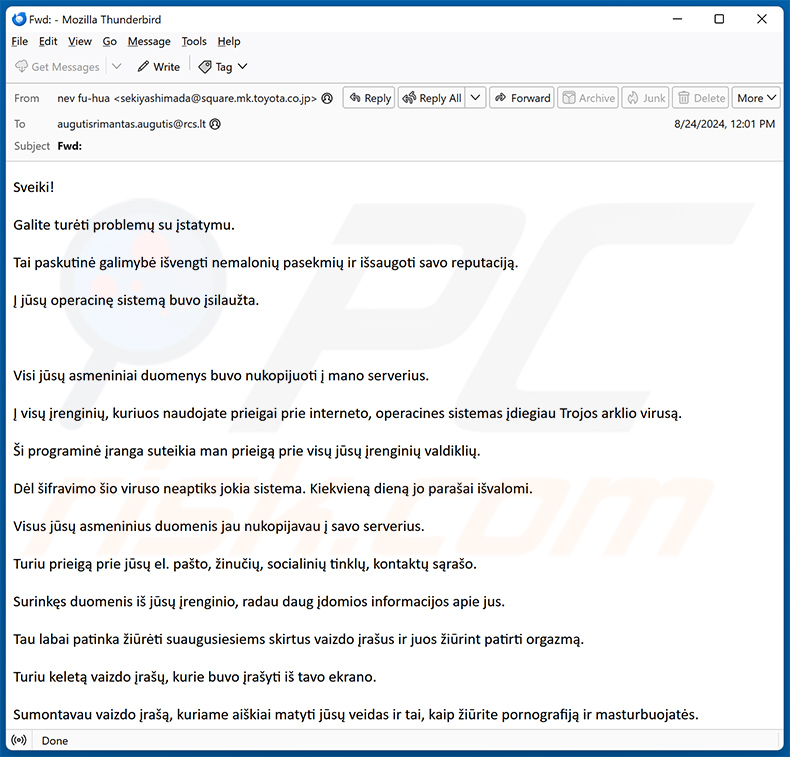
Text presented within:
Subject: Fwd:
Sveiki!Galite turėti problemų su įstatymu.
Tai paskutinė galimybė išvengti nemalonių pasekmių ir išsaugoti savo reputaciją.
Į jūsų operacinę sistemą buvo įsilaužta.
Visi jūsų asmeniniai duomenys buvo nukopijuoti į mano serverius.
Į visų įrenginių, kuriuos naudojate prieigai prie interneto, operacines sistemas įdiegiau Trojos arklio virusą.
Ši programinė įranga suteikia man prieigą prie visų jūsų įrenginių valdiklių.
Dėl šifravimo šio viruso neaptiks jokia sistema. Kiekvieną dieną jo parašai išvalomi.
Visus jūsų asmeninius duomenis jau nukopijavau į savo serverius.
Turiu prieigą prie jūsų el. pašto, žinučių, socialinių tinklų, kontaktų sąrašo.
Surinkęs duomenis iš jūsų įrenginio, radau daug įdomios informacijos apie jus.
Tau labai patinka žiūrėti suaugusiesiems skirtus vaizdo įrašus ir juos žiūrint patirti orgazmą.
Turiu keletą vaizdo įrašų, kurie buvo įrašyti iš tavo ekrano.
Sumontavau vaizdo įrašą, kuriame aiškiai matyti jūsų veidas ir tai, kaip žiūrite pornografiją ir masturbuojatės.
Jūsų šeima ir draugai neturės problemų atpažindami jus šiame vaizdo įraše. Šis vaizdo įrašas gali visiškai sugriauti jūsų reputaciją.
Be to, jūsų įrenginyje sugebėjau rasti duomenų, kuriuos jūsų šalyje saugoti draudžiama.
Galite turėti problemų su įstatymais.Galiu išsiųsti jūsų neteisėtos veiklos įrodymus visiems jūsų kontaktams, paviešinti juos visiems internete.
Turiu daug jūsų asmeninių duomenų. Tai jūsų naršymo istorija, "Messenger" ir socialinės žiniasklaidos susirašinėjimas, telefono skambučiai, asmeninės nuotraukos ir vaizdo įrašai.
Visus jūsų duomenis galiu paskelbti viešai.Esu tikras, kad po to jumis susidomės policija. Ir kitos jūsų šalies saugumo tarnybos.
Užtenka vieno mano pelės spustelėjimo, kad visa jūsų įrenginyje saugoma informacija taptų vieša.
Jūs suprantate pasekmes.Tai bus tikra katastrofa.
Jūsų gyvenimas bus sugriautas.Esu tikras, kad norėtumėte to išvengti, ar ne?
Tai labai paprasta.Jums reikia pervesti man 1000 eurų (bitkoinų ekvivalentu pagal pervedimo metu galiojantį kursą). Po to ištrinsiu visą informaciją apie jus iš savo serverių.
Daugiau jūsų nebetrukdysiu.
Mano Bitcoin piniginė mokėjimui: 1JhZd6jfvfwJahTTLSsRpUh6o53qCmajLNežinote, kas yra bitkoinai ir kaip jais naudotis? Pasinaudokite "Google".
Mokėjimui atlikti turite 2 darbo dienas.
Perskaičius šį laišką, laikmatis prasideda automatiškai.Jau gavau pranešimą, kad atidarėte šį el. laišką.
Atsakyti man nereikia, šis el. laiškas buvo sukurtas automatiškai ir jo neįmanoma atsekti.
Nereikia bandyti su kuo nors susisiekti ir prašyti pagalbos. Bitkoinų piniginė yra nesusekama, todėl tik švaistysite laiką.
Policija ir kitos saugumo tarnybos jums taip pat nepadės.
Kiekvienu iš šių atvejų nedelsdamas paskelbsiu visus vaizdo įrašus.
Visi jūsų duomenys jau nukopijuoti į mano serverių klasterį, todėl el. pašto ar socialinės žiniasklaidos slaptažodžių keitimas nepadės.
Tikiuosi, kad pasirinksite tinkamą sprendimą.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is "I Compromised Your Operating System" sextortion scam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
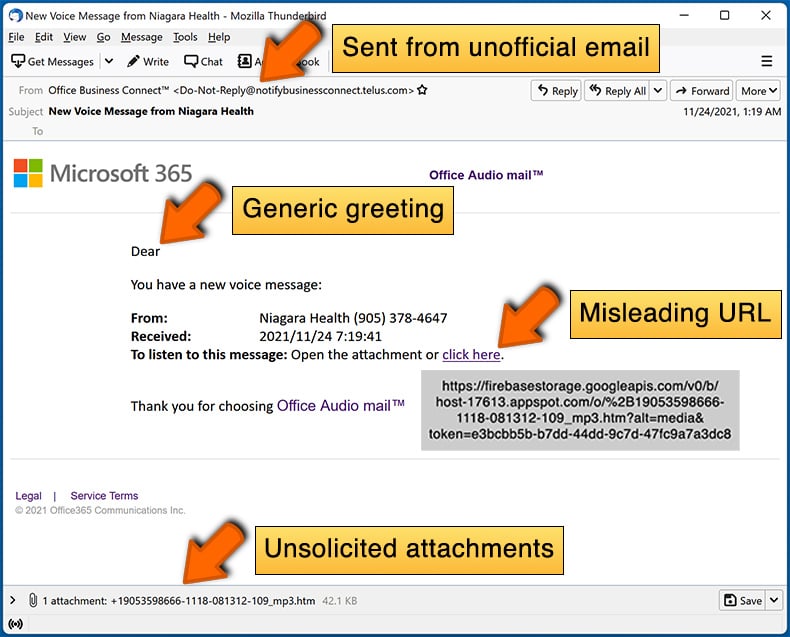
How to spot a malicious email?
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:
What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
Spam emails are not personal, even if they include details relevant to the recipients. Cyber criminals distribute these emails by the thousand with the hopes that at least some recipients will fall for their scams.
Was my computer actually hacked and does the sender have any information?
No, none of your devices were infected by the sender. Neither has the scammer made recordings of you or acquired any other private information.
How did cyber criminals get my email password?
Sending sextortion emails from the recipient's very own mail account gives credence to the scam. Typically, email log-in credentials are stolen through phishing scams (e.g., fake sign-in webpages, registration forms, etc.). The threat of falling victim to such a scam is increased by using the same passwords for multiple accounts; hence, the log-in credentials for an email could have been obtained through a different compromised account.
The less likely scenario is that scammers may have acquired this information by breaching the recipient's devices. And the most unlikely scenario would be a data breach on a service provider's end.
I have sent cryptocurrency to the address presented in this email, can I get my money back?
No, the transferred funds cannot be retrieved due to the nearly untraceable nature of cryptocurrency transactions.
I have provided my personal information when tricked by a spam email, what should I do?
If you have provided your log-in credentials – immediately change the passwords of all potentially exposed accounts and inform their official support. And if you've disclosed other private data (e.g., ID card details, passport photos/scans, credit card numbers, etc.) – contact the appropriate authorities without delay.
I have read a spam email but didn't open the attachment, is my computer infected?
Devices are infected when malicious attachments/links are opened; merely reading an email poses no such threat.
I have downloaded and opened a file attached to a spam email, is my computer infected?
If the opened file was an executable (.exe, .run, etc.) – most likely, yes – your system was infected. However, you might have avoided an infection if it was a document (.doc, .xls, .pdf, .one, etc.). Some of these formats may require additional user interaction to jumpstart malware download/installation chains (e.g., enabling macro commands, clicking embedded files/links, etc.).
Will Combo Cleaner remove malware infections present in email attachments?
Yes, Combo Cleaner is designed to eliminate all manner of threats. It can detect and remove most of the known malware infections. Note that running a full system scan is paramount since sophisticated malicious programs usually hide deep within systems.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion