Get free scan and check if your device is infected.
Remove it nowTo use full-featured product, you have to purchase a license for Combo Cleaner. Seven days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
What kind of malware is Cryxos?
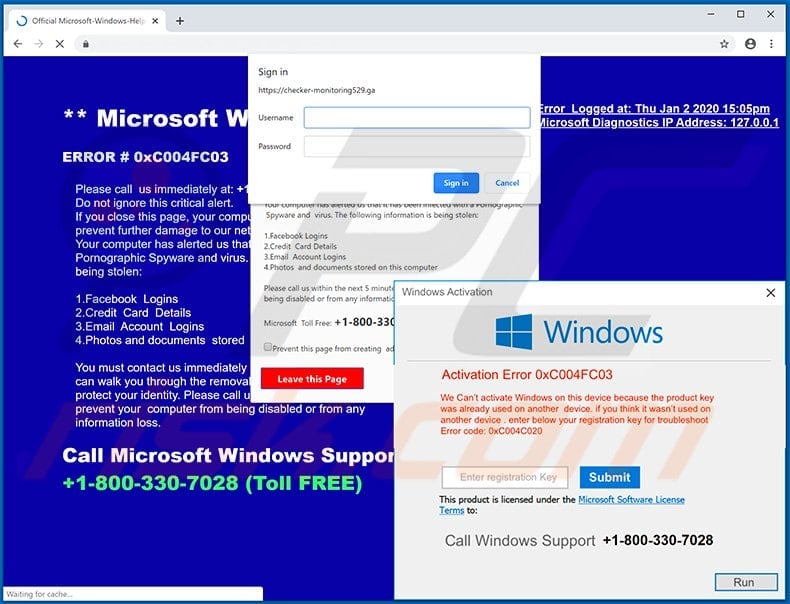
Cryxos Trojans display deceptive alerts/notifications on compromised or malicious websites. The notifications claim that the user's computer is infected with a virus (or viruses), is blocked, and some personal details have been stolen. In most cases, users are encouraged to solve the problem by calling scammers via the telephone number provided.
Generally, Cryxos Trojans display messages that are disguised as legitimate notifications from Microsoft, however, this company has nothing to do with these technical support scams. Do not trust these scams and remove Cryxos from the operating system immediately.
More about Cryxos
In most cases, Cryxos Trojans display virus/error alerts when users open malicious or compromised websites that are injected with a malicious JavaScript file. The script displays various notifications disguised as legitimate messages from Microsoft or the Windows Operating System.
Typically, the messages claim that the operating system is infected with a virus (or multiple viruses) and encourage users to call a certain number for technical support. The messages claim that the user's computer is blocked and that personal information (e.g., banking-related details) has been stolen.
In some cases, Cryxos Trojans play an audio recording repeating the same message that is displayed in the alert notifications. In any case, all of these notifications are fake and should never be trusted. Generally, scammers seek to trick users into believing that they must solve a problem that has arisen (i.e., remove viruses, fix errors, etc.) by calling the number provided immediately.
Typically, scammers try to extort money from unsuspecting visitors by encouraging them to use their online "technical services" or purchase software. They try to trick users into paying for their so-called "assistance". The scammers sometimes ask users to give remote access to their computers.
Granting such access allows scammers to take a full control of their computers. Therefore, scammers can access personal information and files, or even infect systems with malicious software such as ransomware.
| Name | Cryxos virus |
| Threat Type | Phishing, Scam, Social Engineering, Fraud. |
| Fake Claim | Typically, tech support scams claim that the user's computer is infected, blocked, or some personal information has been stolen. |
| Tech Support Scammer Phone Number | +1-800-330-7028, +1-855-723-3755, +1-800-278-6064, +1-833-272-0272, +1-844-919-5111 |
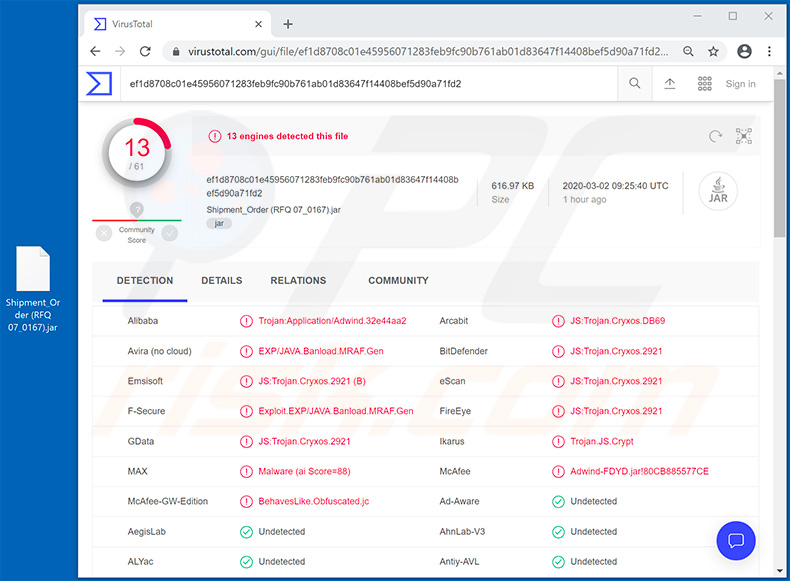
| Detection Names (malicious attachment) |
Arcabit (JS:Trojan.Cryxos.DB69), BitDefender (JS:Trojan.Cryxos.2921), Emsisoft (JS:Trojan.Cryxos.2921 (B)), Adwind (Adwind-FDYD.jar!80CB885577CE), Full List Of Detections (VirusTotal) |
| Symptoms | Fake error messages, fake system warnings, pop-up errors, hoax computer scan. |
| Distribution methods | Compromised websites, rogue online pop-up ads, potentially unwanted applications. |
| Damage | Loss of sensitive private information, monetary loss, identity theft, possible malware infections. |
| Malware Removal (Windows) |
To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. Download Combo CleanerTo use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com. |
Examples of technical support scams
Some examples of tech support scams include "This is a VIRUS. You computer is blocked", "Activation Error 0xC004FC03" and "CRITICAL_PROCESS_DIED". All attempt to trick users into believing that they need to contact (typically, call) scammers and use their services and/or software immediately.
Scammers behind these scams generate revenue by deceiving users into paying for supposedly legitimate services and/or software.
Generally, people do not visit websites, which display these fake virus alert/error and other similar notifications, intentionally. In most cases, the sites are opened through other untrusted web pages, deceptive advertisements or certain unwanted applications installed on browsers and/or operating systems.
How did unwanted applications install on my computer?
Developers often distribute such apps by including them into the download/installation set-ups of other programs. This distribution method is called "bundling". Typically, information about additional downloads and installations can be found in "Custom", "Advanced" and other settings of the set-ups.
Many people fail to check and change these settings, thereby agreeing by default with offers to download or install additionally-included software. Unwanted downloads and installations can also be caused when people click deceptive ads that execute certain scripts. These dangerous ads are generally displayed on untrusted websites.
How to avoid installation of unwanted applications
Download all files and programs from official and trustworthy websites, and via direct download links. Other channels, tools such as third party downloaders, Peer-to-Peer networks (e.g., eMule, torrent clients), unofficial websites, etc., should not be used.
Check all "Custom", "Advanced" and other similar settings - decline offers to download or install unwanted apps before completing the process. It is not safe to click ads shown on dubious web pages - they can open other sites of this kind or cause download/installation of unwanted software.
To stop your browser from opening dubious web pages or displaying ads, remove all unwanted add-ons, plug-ins and extensions. Also remove programs of this kind from the operating system. If your computer is already infected with rogue software, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate them.
Screenshot of a tech support scam ("CRITICAL_PROCESS_DIED"):

Text in this scam:
Windows Security
Microsoft Edge
The server ****** is asking for your user name and password.That server also reports:
"__________
System_Protect_-_PROTECT_ERROR_0xEB6468728
Contact_Microsoft_Support__+1_(855)_723-3755_Toll-Free.
__________".
Microsoft Edge
Stop code: CRITICAL_PROCESS_DIED | Error Report
Security system has detected the threatening attempt to gain access to your bank logins and related data, but this dangerous connection was blocked with Firewall and further data leak was prevented.
We strongly recommend you to perform temporary block of all your accounts, and take some necessary security measures.
Despite the timely blocking of the connection, there is still a serious threat of private data stealth.
Please don t wait to respond, every minute is important!
There is possibility that virus already hurt your disks or destroyed and stole its data.
It is reason for checking current system security and verifying its stability.
Do not spend your time and immediately call us or contact our service center support team.
------------
Contact Microsoft Support:
+1 (855) 723-3755
------------
We are waiting for your rapid responce to help you
Please contact our administration to solve this issue.
Call Help Desk:
+1 (855) 723-3755
Screenshot of another tech support scam ("This is a VIRUS. You computer is blocked"):
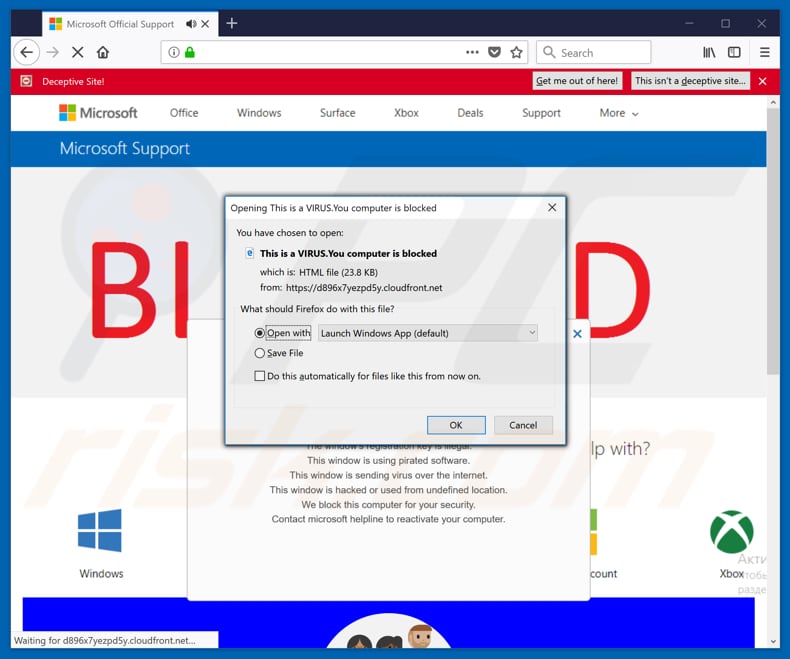
Text in this scam:
VIRUS ALERT FROM MICROSOFT
This computer is BLOCKED
Do not close this window and restart your computer
Your computer's registration key is Blocked.
Why we blocked your computer?
The window's registration key is illegal.
This window is using pirated software.
This window is sending virus over the internet.
This window is hacked or used from undefined location.
We block this computer for your security.
Contact microsoft helpline to reactivate your computer.
Microsoft Security Tollfree:
+1-800-278-6064
Prevent this page from creating additional dialogues.
Windows Support Alert
Your System Detected Some Unusual Activity.
It might harm your computer data and track your financial activities.
Please report this activity to +1-800-278-6064
Ignore Alert Chat Now
Enter Windows registration key to unblock.
ENTER KEY:
Screenshot of another tech support scam ("VIRAL ALARM OF MICROSOFT"):
Text in this scam:
VIRAL ALARM OF MICROSOFT
***This computer is BLOCKED***
Do not close this window and restart your computer
The registry key on your computer is Blocked.
Why did we block your computer?
The registry key of the window is illegal.
This window uses pirated software.
This window sends virus over the internet.
This window is hacked or used from undefined location.
We block this computer for your safety.
Contact Windows helpline to wake up your computer.
Enter Windows registration key to unlock or call
+1-833-272-0272(Toll-free)
ENTER KEY:Windows Support alarm
Your System Has Discovered An Unusual Activity.
It could harm your computer data and your financial activities.
Please report this activity an +1-833-272-0272
Ignore warning
Chat Well
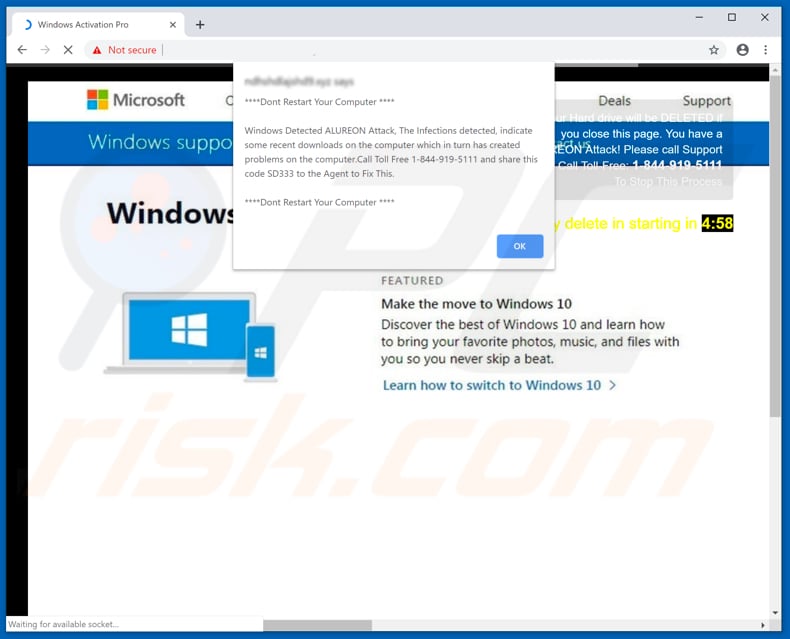
One more example of a tech support scam ("Windows Detected ALUREON Attack"):
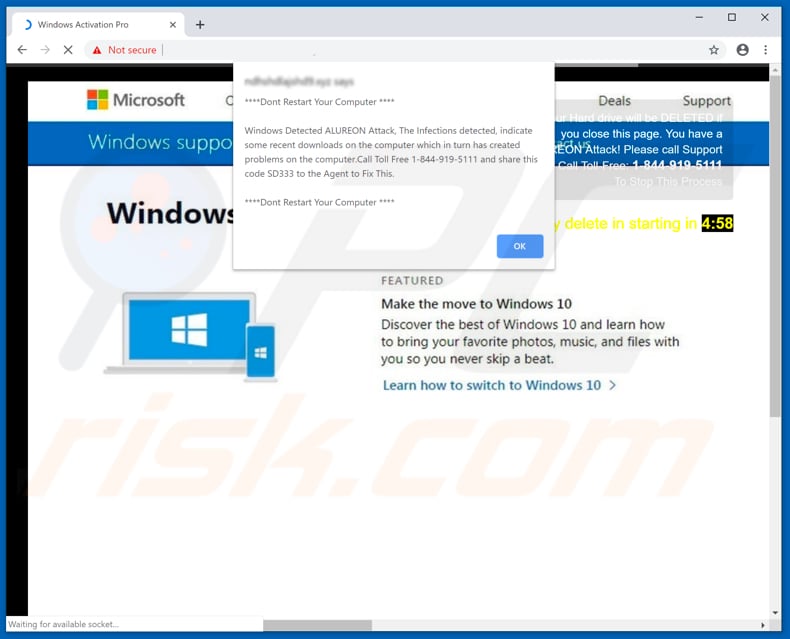
Text in this scam:
Windows Detected ALUREON Attack, The infections detected, indicate some recent downloads on the computer which in turn has created problems on the computer. Call Toll Free 1-844-919-5111 and share this code SD333 to the Agent to Fix This.
Example of a spam email used to promote Cryxos trojan:
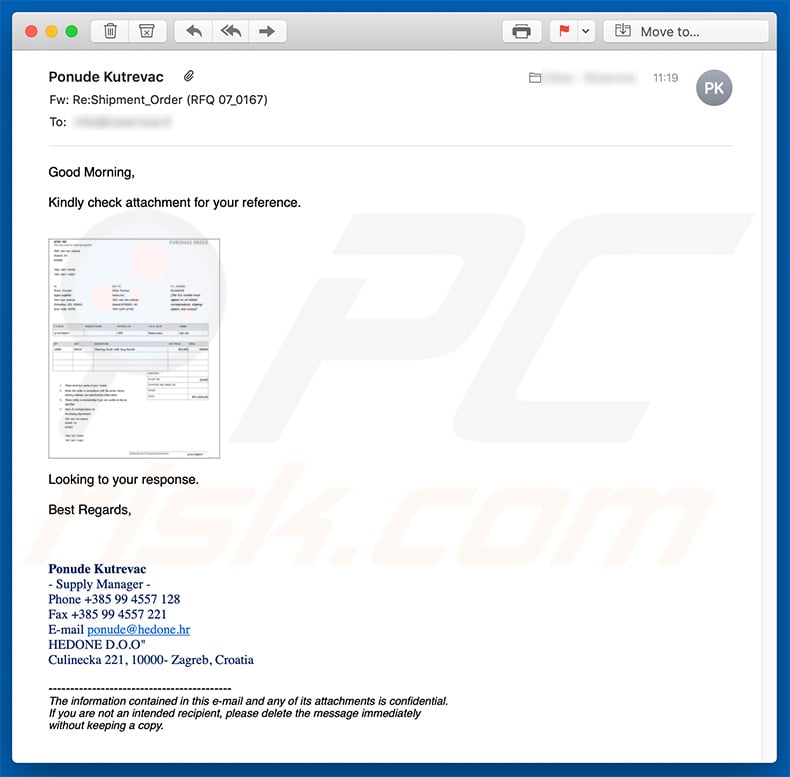
Text presented within this email:
Subject: Re:Shipment_Order (RFQ 07_0167)
Good Morning,
Kindly check attachment for your reference.
Looking to your response.
Best Regards,
Ponude Kutrevac
- Supply Manager -
Phone +385 99 4557 128
Fax +385 99 4557 221
E-mail ponude@hedone.hr
HEDONE D.O.O"
Culinecka 221, 10000- Zagreb, Croatia
-----
The information contained in this e-mail and any of its attachments is confidential.
If you are not an intended recipient, please delete the message immediately
without keeping a copy.
Screenshot of malicious attachment ("Shipment_Order (RFQ 07_0167).jar") detections in VirusTotal:
Example of another spam email used to spread Cryxos trojan (the PDF icon is an image with a link leading to .gz archive download):

Text presented within:
Please quote as per the attached requirements and specifications,
Please quote asap as this is needed Top Urgent.
Thanks in advance.
Best regards,
Peter Mickens
Parts & Procurement
Precision Air,Inc
500 South McCall Blvd
Florence, SC 29506
M-F: 3:70am-4pm
O 1(843) 779-9345
req-allparts.com
info@req-allparts.com
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
DOWNLOAD Combo CleanerBy downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Quick menu:
- What is Cryxos Trojan?
- STEP 1. Uninstall deceptive applications using Control Panel.
- STEP 2. Remove adware from Internet Explorer.
- STEP 3. Remove rogue extensions from Google Chrome.
- STEP 4. Remove potentially unwanted plug-ins from Mozilla Firefox.
- STEP 5. Remove rogue extensions from Safari.
- STEP 6. Remove rogue plug-ins from Microsoft Edge.
Removal of potentially unwanted applications:
Windows 11 users:
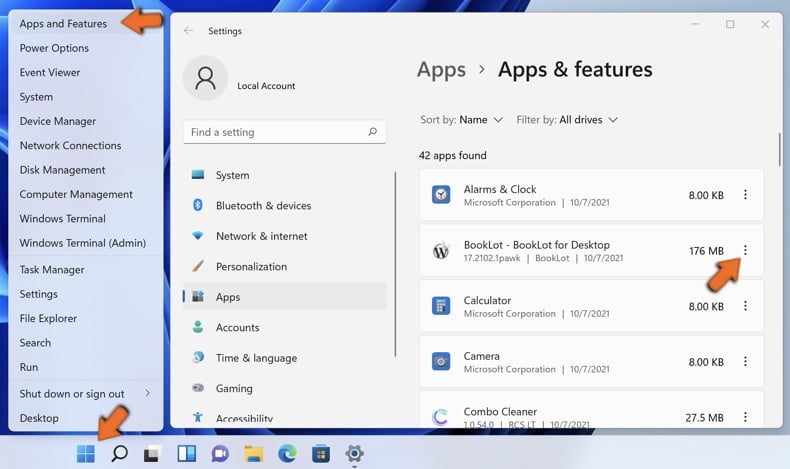
Right-click on the Start icon, select Apps and Features. In the opened window search for the application you want to uninstall, after locating it, click on the three vertical dots and select Uninstall.
Windows 10 users:
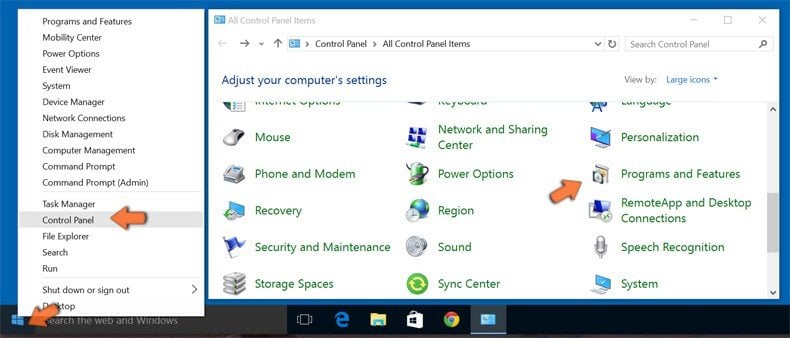
Right-click in the lower left corner of the screen, in the Quick Access Menu select Control Panel. In the opened window choose Programs and Features.
Windows 7 users:

Click Start (Windows Logo at the bottom left corner of your desktop), choose Control Panel. Locate Programs and click Uninstall a program.
macOS (OSX) users:

Click Finder, in the opened screen select Applications. Drag the app from the Applications folder to the Trash (located in your Dock), then right click the Trash icon and select Empty Trash.

In the uninstall programs window, look for any suspicious/recently-installed applications, select these entries and click "Uninstall" or "Remove".
After uninstalling the potentially unwanted application, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
DOWNLOAD remover for malware infections
Combo Cleaner checks if your computer is infected with malware. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by RCS LT, the parent company of PCRisk.com.
Remove rogue extensions from Internet browsers:
Video showing how to remove potentially unwanted browser add-ons:
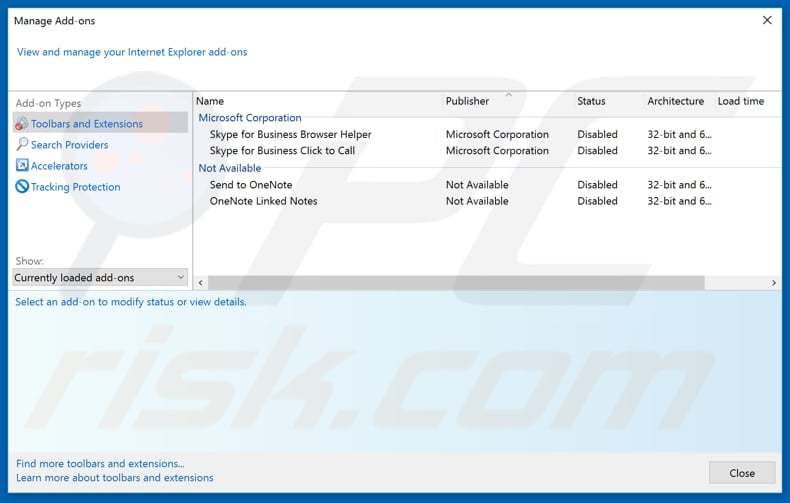
 Remove malicious add-ons from Internet Explorer:
Remove malicious add-ons from Internet Explorer:

Click the "gear" icon ![]() (at the top right corner of Internet Explorer), select "Manage Add-ons". Look for any recently-installed suspicious browser extensions, select these entries and click "Remove".
(at the top right corner of Internet Explorer), select "Manage Add-ons". Look for any recently-installed suspicious browser extensions, select these entries and click "Remove".
Optional method:
If you continue to have problems with removal of the cryxos virus, reset your Internet Explorer settings to default.
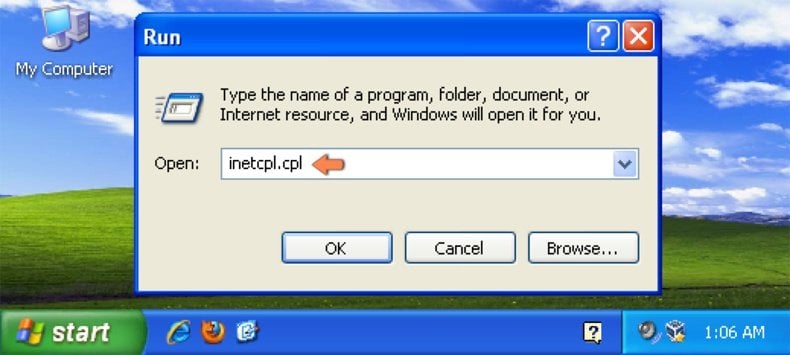
Windows XP users: Click Start, click Run, in the opened window type inetcpl.cpl In the opened window click the Advanced tab, then click Reset.
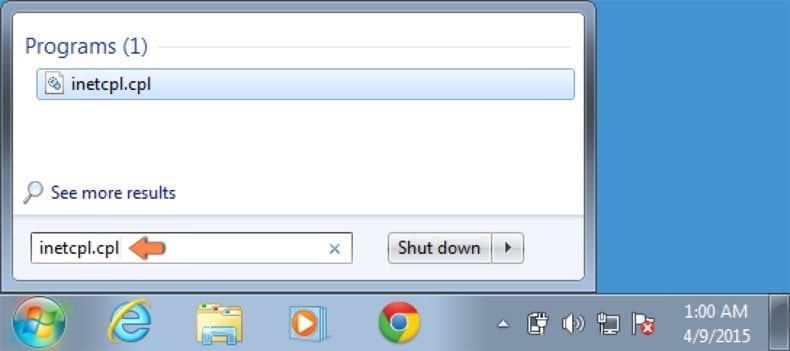
Windows Vista and Windows 7 users: Click the Windows logo, in the start search box type inetcpl.cpl and click enter. In the opened window click the Advanced tab, then click Reset.
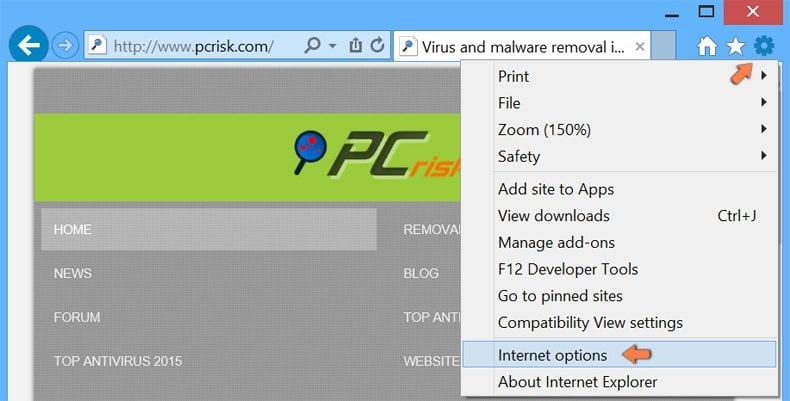
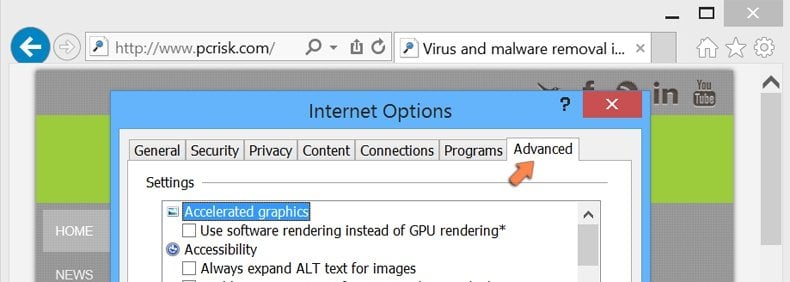
Windows 8 users: Open Internet Explorer and click the gear icon. Select Internet Options.
In the opened window, select the Advanced tab.
Click the Reset button.
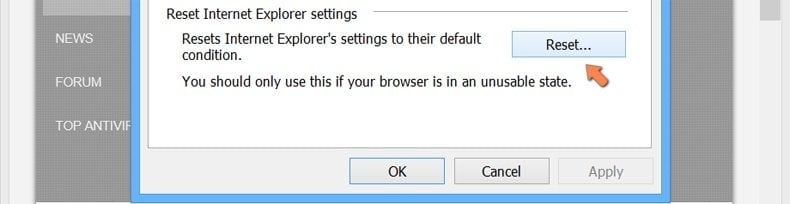
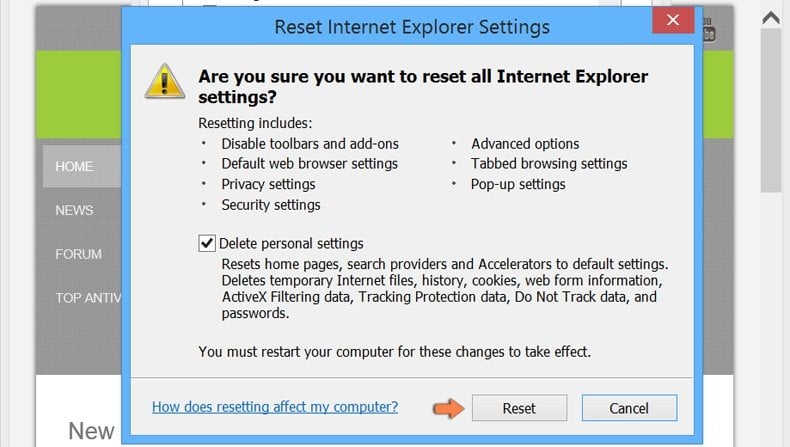
Confirm that you wish to reset Internet Explorer settings to default by clicking the Reset button.
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:

Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate all recently-installed suspicious browser add-ons and remove them.
(at the top right corner of Google Chrome), select "More tools" and click "Extensions". Locate all recently-installed suspicious browser add-ons and remove them.

Optional method:
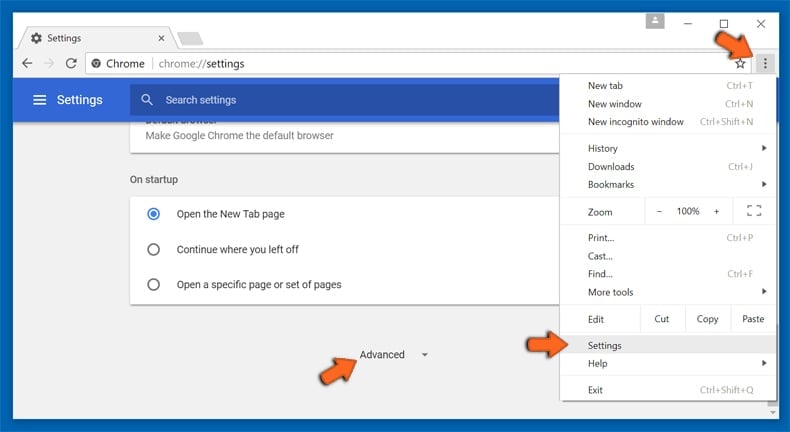
If you continue to have problems with removal of the cryxos virus, reset your Google Chrome browser settings. Click the Chrome menu icon ![]() (at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
(at the top right corner of Google Chrome) and select Settings. Scroll down to the bottom of the screen. Click the Advanced… link.
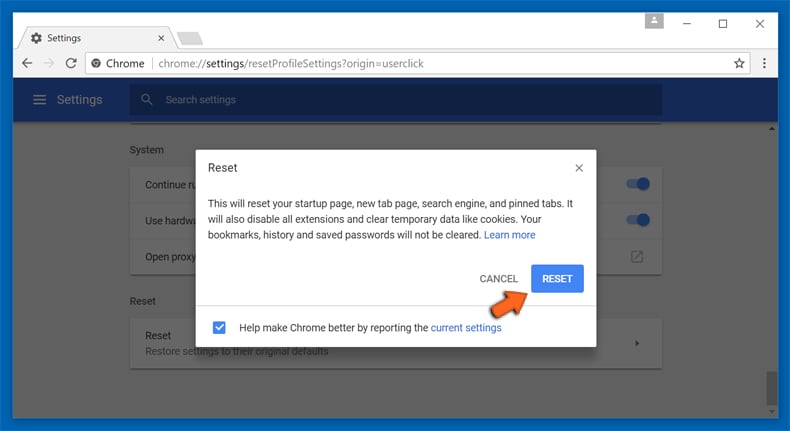
After scrolling to the bottom of the screen, click the Reset (Restore settings to their original defaults) button.
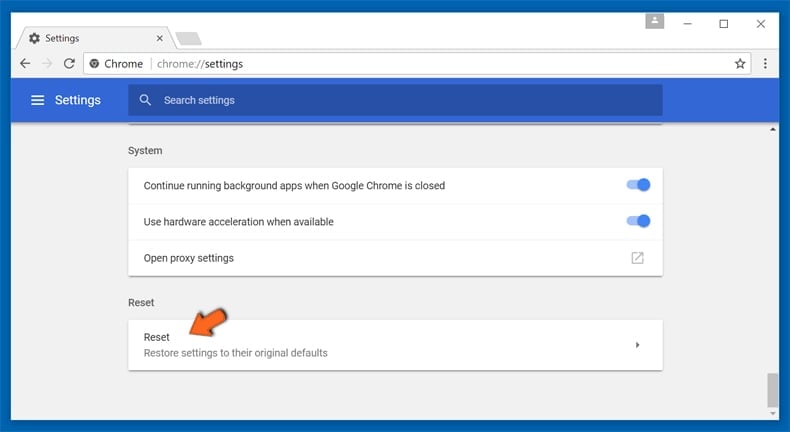
In the opened window, confirm that you wish to reset Google Chrome settings to default by clicking the Reset button.
 Remove malicious plug-ins from Mozilla Firefox:
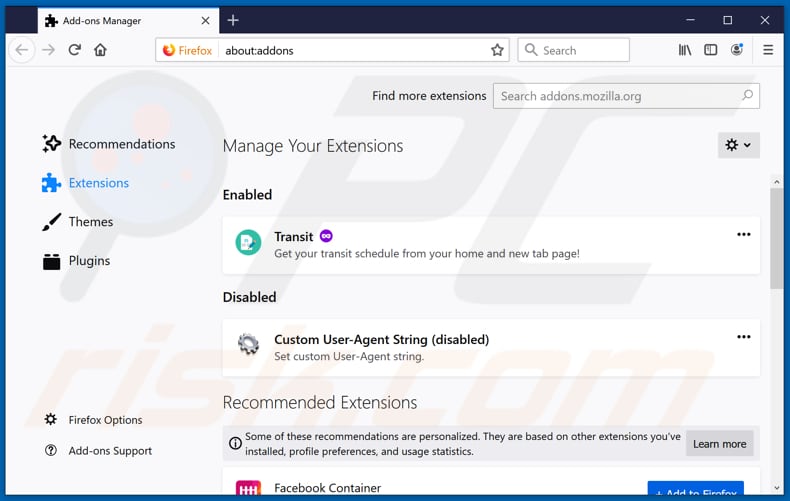
Remove malicious plug-ins from Mozilla Firefox:

Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons". Click on "Extensions", in the opened window remove all recently-installed suspicious browser plug-ins.
(at the top right corner of the main window), select "Add-ons". Click on "Extensions", in the opened window remove all recently-installed suspicious browser plug-ins.
Optional method:
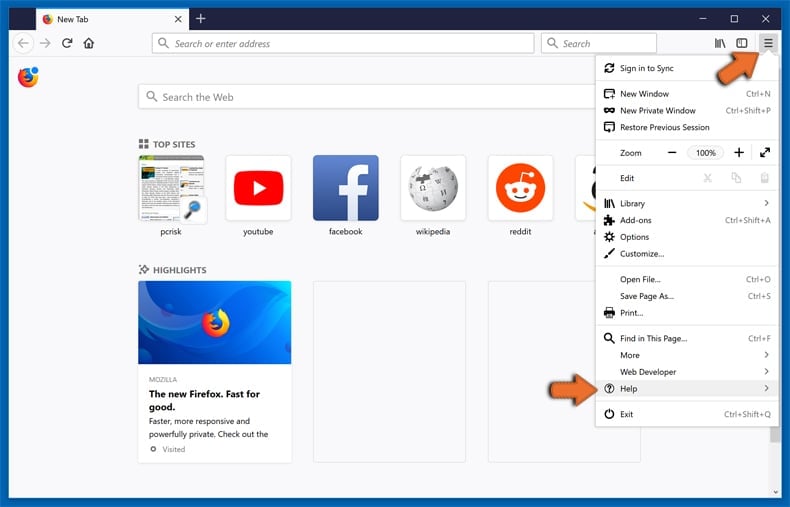
Computer users who have problems with cryxos virus removal can reset their Mozilla Firefox settings.
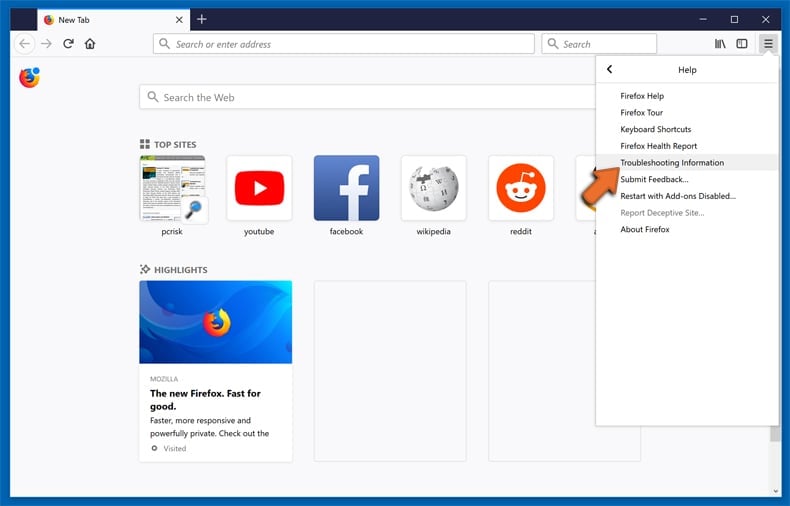
Open Mozilla Firefox, at the top right corner of the main window, click the Firefox menu, ![]() in the opened menu, click Help.
in the opened menu, click Help.
Select Troubleshooting Information.
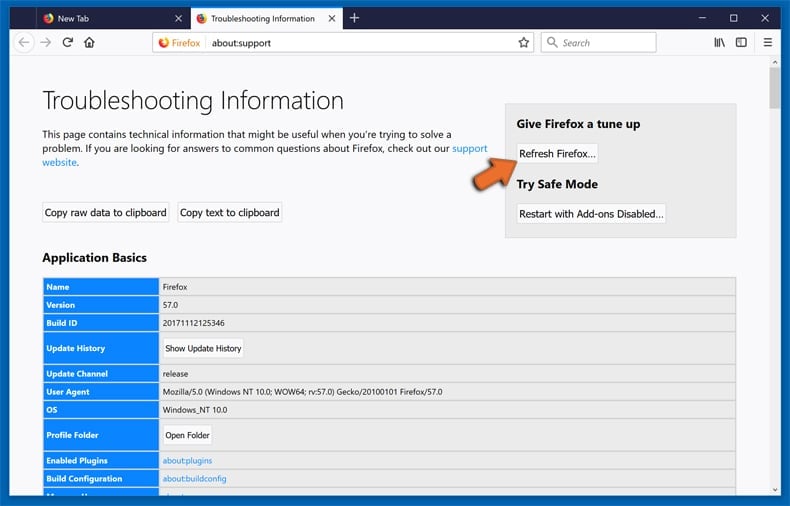
In the opened window, click the Refresh Firefox button.
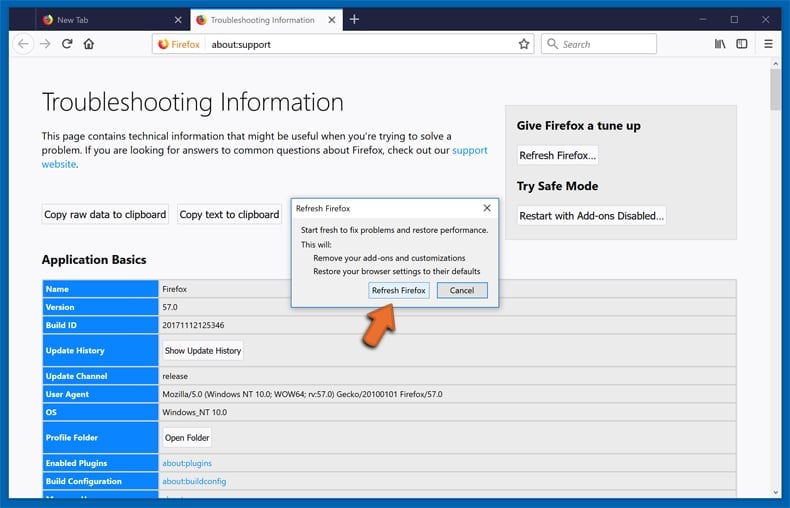
In the opened window, confirm that you wish to reset Mozilla Firefox settings to default by clicking the Refresh Firefox button.
 Remove malicious extensions from Safari:
Remove malicious extensions from Safari:
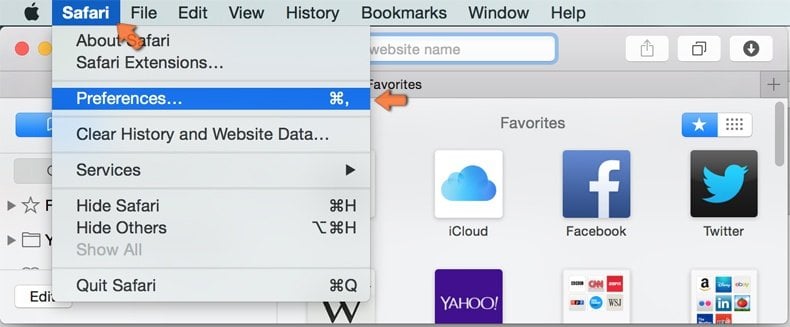
Make sure your Safari browser is active, click Safari menu, and select Preferences....

In the opened window click Extensions, locate any recently installed suspicious extension, select it and click Uninstall.
Optional method:
Make sure your Safari browser is active and click on Safari menu. From the drop down menu select Clear History and Website Data...
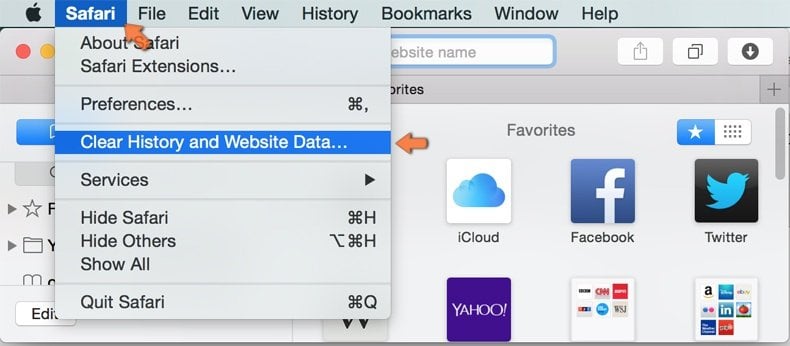
In the opened window select all history and click the Clear History button.

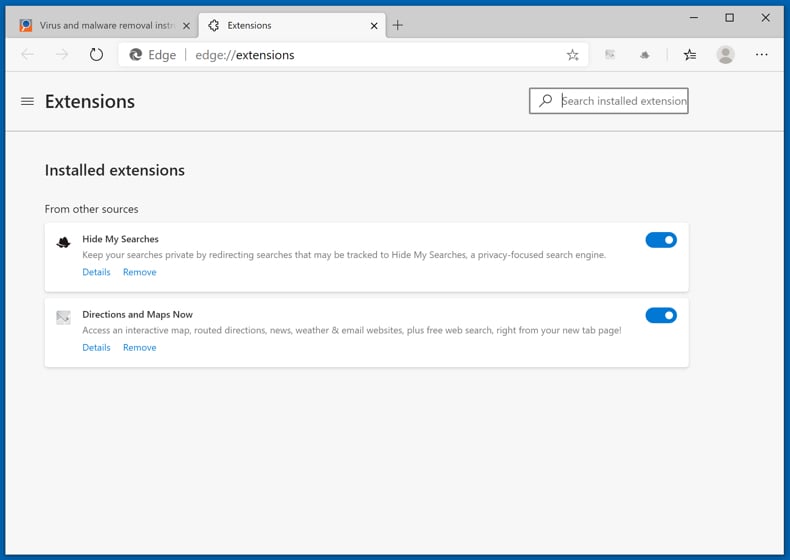
 Remove malicious extensions from Microsoft Edge:
Remove malicious extensions from Microsoft Edge:
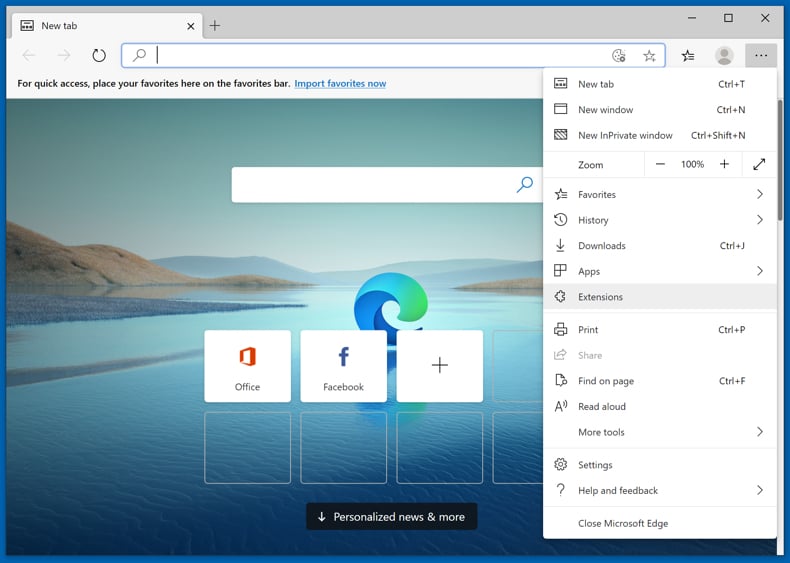
Click the Edge menu icon ![]() (at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
(at the upper-right corner of Microsoft Edge), select "Extensions". Locate all recently-installed suspicious browser add-ons and click "Remove" below their names.
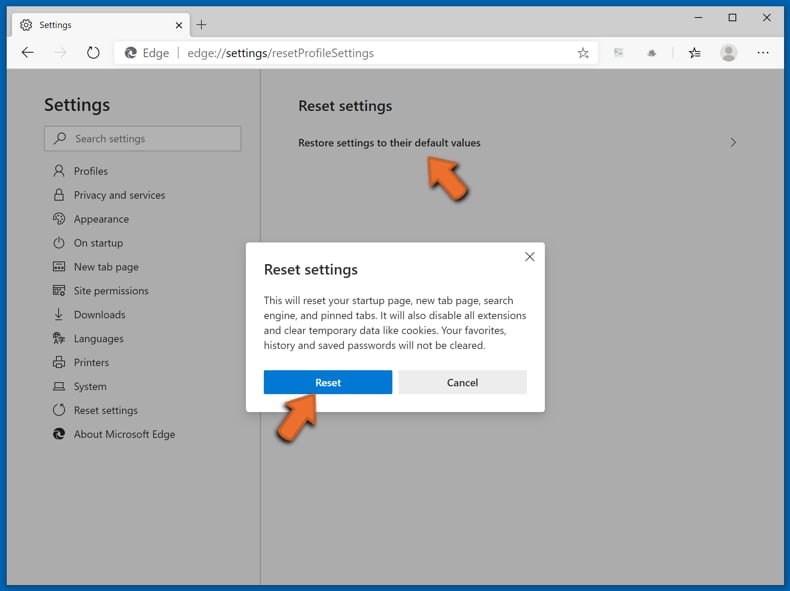
Optional method:
If you continue to have problems with removal of the cryxos virus, reset your Microsoft Edge browser settings. Click the Edge menu icon ![]() (at the top right corner of Microsoft Edge) and select Settings.
(at the top right corner of Microsoft Edge) and select Settings.
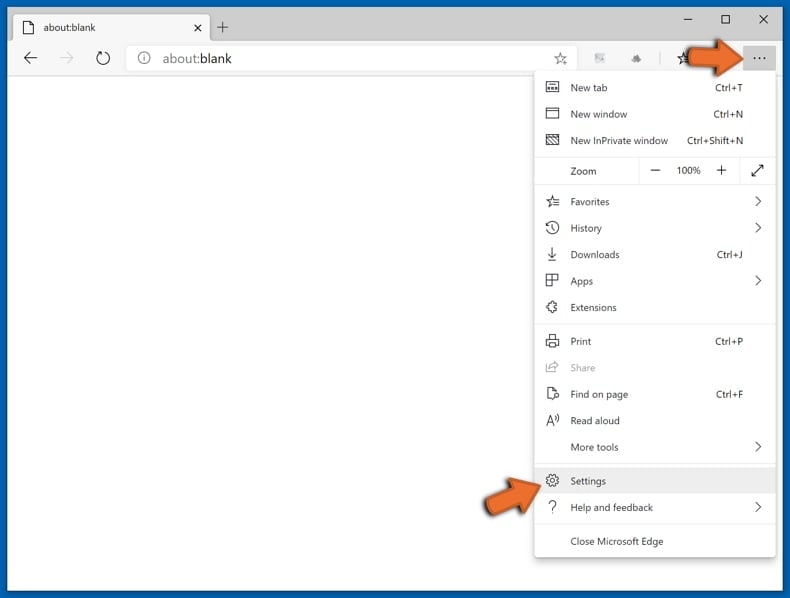
In the opened settings menu select Reset settings.
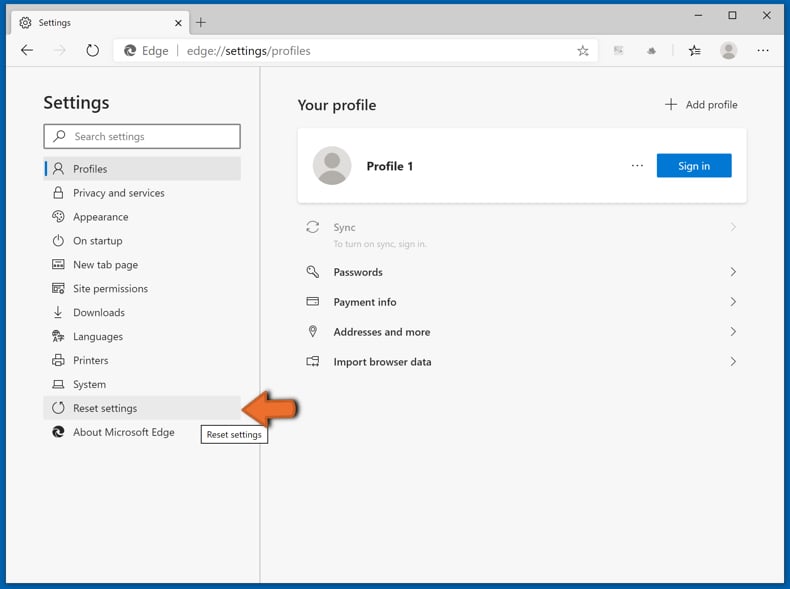
Select Restore settings to their default values. In the opened window, confirm that you wish to reset Microsoft Edge settings to default by clicking the Reset button.
- If this did not help, follow these alternative instructions explaining how to reset the Microsoft Edge browser.
Summary:
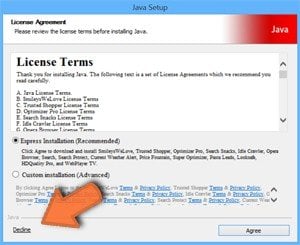 Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Commonly, adware or potentially unwanted applications infiltrate Internet browsers through free software downloads. Note that the safest source for downloading free software is via developers' websites only. To avoid installation of adware, be very attentive when downloading and installing free software. When installing previously-downloaded free programs, choose the custom or advanced installation options – this step will reveal any potentially unwanted applications listed for installation together with your chosen free program.
Post a comment:
If you have additional information on cryxos virus or it's removal please share your knowledge in the comments section below.
Frequently Asked Questions (FAQ)
What is a pop-up scam?
A pop-up scam is a fake message (e.g., virus alert, system warning, error notification) designed to trick page visitors into performing certain actions.
What is the purpose of a pop-up scam?
In most cases, scams of this type are used to extract sensitive information or money. Also, they are used to trick visitors into providing remote access to computers or even downloading (and executing) malware.
Why do I encounter fake pop-ups?
These pop-ups are displayed by installed rogue software (like Cryxos) and websites that use rogue advertising networks.
Will Combo Cleaner protect me from pop-up scams?
Combo Cleaner will scan visited sites and detect malicious ones, including pages that display deceptive pop-ups. This application will warn you about untrustworthy pages and restrict access to them.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.
PCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
DonatePCrisk security portal is brought by a company RCS LT.
Joined forces of security researchers help educate computer users about the latest online security threats. More information about the company RCS LT.
Our malware removal guides are free. However, if you want to support us you can send us a donation.
Donate
▼ Show Discussion