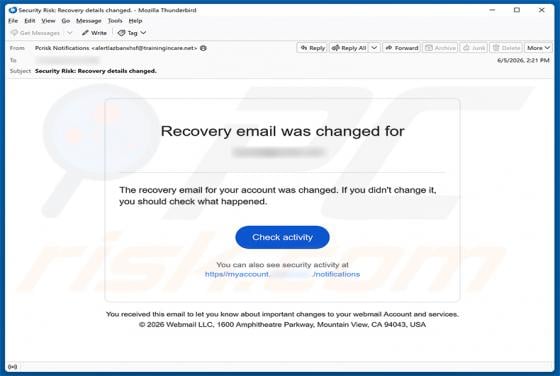
Recovery Email Was Changed Scam
We examined this email and determined it is a phishing scam. Disguised as a security alert from a webmail service, it falsely claims that the recipient's recovery email address was changed. Scammers use it to trick recipients into handing over their login credentials on a fake website. Thi