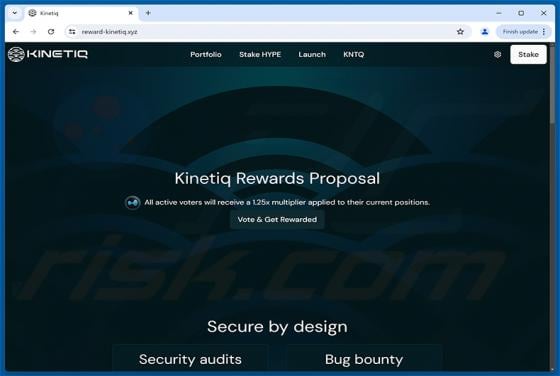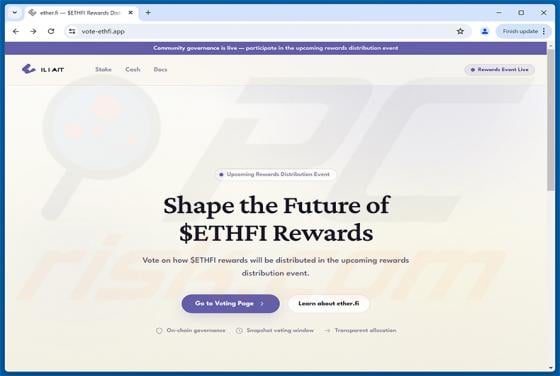
$ETHFI Vote Rewards Scam
We have inspected the website vote-ethfi[.]app and found that it imitates the official ether.fi platform, presenting a fake "$ETHFI Rewards Allocation Proposal" governance vote. The page is designed to trick visitors into connecting their cryptocurrency wallets, which can lead to the theft of digi