How to eliminate the Cuckoo malware from your Mac
![]() Written by Tomas Meskauskas on (updated)
Written by Tomas Meskauskas on (updated)
What kind of malware is Cuckoo?
Cuckoo is a Mac-specific malware that operates as spyware and an information-stealer. It can record information and extract data from various browsers, cryptocurrency wallets, FTP clients, messengers, and other apps.
The Cuckoo malicious program has been around since at least the spring of 2024. This malware was observed being proliferated via trojanized applications for converting audio from steaming platforms into downloadable MP3 files.

Cuckoo malware overview
As mentioned in the introduction, Cuckoo has been noted infiltrating devices under the guise of a streaming platform MP3 converter (e.g., DumpMedia Spotify Music Converter). The malware is installed in an application bundle, which can include legitimate software.
Typically, installation on Mac systems requires users to drag software into the /Applications folder. However, the investigated Cuckoo sample instructed to "Right Click on the icon below" (i.e., "DumpMedia Spotify Music Converter") and "Click open". Further user interaction may be necessary, such as granting the malware various permissions.
The victim can also be asked to provide their password. This technique is often used to collect said log-in credentials, but in the case of Cuckoo – it tests the validity of the password as well. User log-in credentials can then be utilized by the malicious software to escalate its privileges. Additionally, Cuckoo uses persistence-ensuring mechanisms.
Following successful infiltrating, this program obtains geolocation data by checking the system's language settings. The data is then used to determine whether to proceed with the infection. At the time of research, the following regions were exempted (i.e., Cuckoo did not continue with the malicious activity for devices based in): Ukraine, Armenia, Belarus, Kazakhstan, and Russia.
If it is decided to go through with the infection, the malware gathers relevant device details, e.g., information relating to hardware, macOS information, device name, username, running processes, installed applications, etc.
Cuckoo can browse and exfiltrate content from the finder, desktop, microphone, and downloads directories. It can steal files based on formats, including documents, spreadsheets, images, databases, etc. (full list below).
This stealer can collect data from folders associated with various applications, such as browsers, cryptowallets, FTP (File Transfer Protocol) clients, VPN (Virtual Private Network) programs, messengers, email clients, gaming-related software, and so on (known targets listed below).
Cuckoo can seek data and apps by keywords (keep in mind that sought content may differ between infections or malware variants).
The program gathers information from Apple software, such as Notes, Keychain (native password management system), and the Safari browser. From Safari, Chromium-based, and Gecko-based browsers – Cuckoo can extract browsing histories, bookmarks, and Internet cookies. The stealer might also target log-in credentials (usernames/passwords) and credit card details stored in these apps.
Cuckoo has the ability to take screenshots, and as it can mute the system volume – this activity can lose its audio cue, thus not raising user suspicion.
It must be mentioned that malware developers often improve upon their creations and methodologies. Therefore, possible future iterations of Cuckoo could have an extended target list or additional/different capabilities.
To summarize, the presence of software like Cuckoo on devices can lead to severe privacy issues, financial losses, and identity theft.
| Name | Cuckoo virus |
| Threat Type | Mac malware, Mac virus, stealer, spyware. |
| Detection Names | Combo Cleaner (Trojan.MAC.Generic.118846), Emsisoft (Trojan.MAC.Generic.118846 (B)), Ikarus (Trojan.OSX.Psw), Kaspersky (HEUR:Trojan-PSW.OSX.Amos.gen), WithSecure (Malware.OSX/AVA.Agent.gours), Full List Of Detections (VirusTotal) |
| Symptoms | Trojans are designed to stealthily infiltrate the victim's computer and remain silent, and thus no particular symptoms are clearly visible on an infected machine. |
| Distribution Methods | Free software installers (bundling), infected email attachments, malicious online advertisements, social engineering, software 'cracks'. |
| Damage | Stolen passwords and banking information, identity theft, the victim's computer added to a botnet. |
| Malware Removal (Mac) | To eliminate possible malware infections, scan your Mac with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
Mac-specific malware examples
PureLand, RustDoor, GoSorry, Activator, and NokNok are just some of our latest articles on malicious programs targeting Mac operating systems.
Malware can have a wide range of capabilities, which are not limited by its classification (e.g., a program designed to cause chain infections could also steal data, etc.).
However, regardless of how malicious software operates – its presence on a system threatens device integrity and user safety. Hence, all threats must be removed immediately upon detection.
How did Cuckoo infiltrate my computer?
Cuckoo has been noted infiltrating systems under the guise of an app for converting music from streaming platforms to MP3 audio files. One known example was named in variants of "DumpMedia Spotify Music Converter".
This malware can infect systems via an application bundle, which may include operational software (e.g., an MP3 converter). The trojanized converter installation setups were promoted through multiple malicious websites, a noteworthy example being the "DumpMedia" domain.
However, other distribution methods are not unlikely. In general, malware is spread by relying on phishing and social engineering techniques. This software is commonly disguised as or bundled with legitimate/regular content.
The most prevalent distribution methods include: dubious download channels (e.g., freeware and free file-hosting websites, Peer-to-Peer sharing networks, etc.), drive-by (stealthy/deceptive) downloads, pirated programs/media, malicious attachments or links in spam emails/messages, online scams, malvertising, illegal software activation tools ("cracks"), and fake updates.
Some malicious programs can even self-proliferate via local networks and removable storage devices (e.g., USB flash drives, external hard drives, etc.).
How to avoid installation of malware?
We strongly recommend downloading only from official and verified sources. Do not use sites offering pirated content (e.g., illegal streaming/downloading, Torrenting, etc.), as these webpages commonly host harmful/malicious software or can lead to websites promoting it (via rogue advertising networks).
Additionally, activate and update programs using functions/tools provided by genuine developers, as those obtained from third-parties (e.g., "cracking" tools, unofficial updates, etc.) can contain malware.
We advise vigilance while browsing since fake and malicious online content usually appears legitimate and innocuous. Another recommendation is to treat incoming emails and other messages with caution. Do not open attachments or links present in suspicious/irrelevant mail, as they can be virulent.
We must emphasize the importance of having a reputable anti-virus installed and kept updated. This software must be used to perform regular system scans and to remove threats and issues. If you believe that your computer is already infected, we recommend running a scan with Combo Cleaner Antivirus for macOS to automatically eliminate infiltrated malware.
Malicious installer proliferating Cuckoo malware:

List of file extensions targeted by Cuckoo malware:
DOC, DOCX, XLS, XLSX, TXT, RTF, PDF, JPG, KEY, PEM, PPK, KDBX, DAT, SQL, ASC, OVPN, RDP, CONT, SON.
Targeted browsers:
- Safari
- Google Chrome
- Mozilla Firefox
- Microsoft Edge
- Opera GX
Targeted miscellaneous software:
- Discord
- Telegram
- Mozilla Thunderbird
- FileZilla
- OpenVPN
- Steam
Targeted cryptocurrency wallets:
- Atomic
- BitPay
- Blockstream
- Coinomi
- Daedalus
- Electron Cash
- Ethereum
- Electrum-LTC
- Exodus
- Guarda
- Jaxx
- Ledger Live
- Monero
- MyMonero
- Trezor
- Wasabi
Update May 16, 2024 - Cuckoo malware has been recently observed being distributed via fake Homebrew download websites. The genuine Homebrew website is brew.sh, meaning that all other domains promoting this app should not be trusted. The same distribution method is also used to spread Atomic Stealer.
Screenshot of a fake Homebrew download website (homebrew[.]cx) used to spread Cuckoo malware:

Instant automatic Mac malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of Mac malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner for Mac
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. Limited seven days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
Video showing how to remove adware and browser hijackers from a Mac computer:
Potentially unwanted applications removal:
Remove potentially unwanted applications from your "Applications" folder:
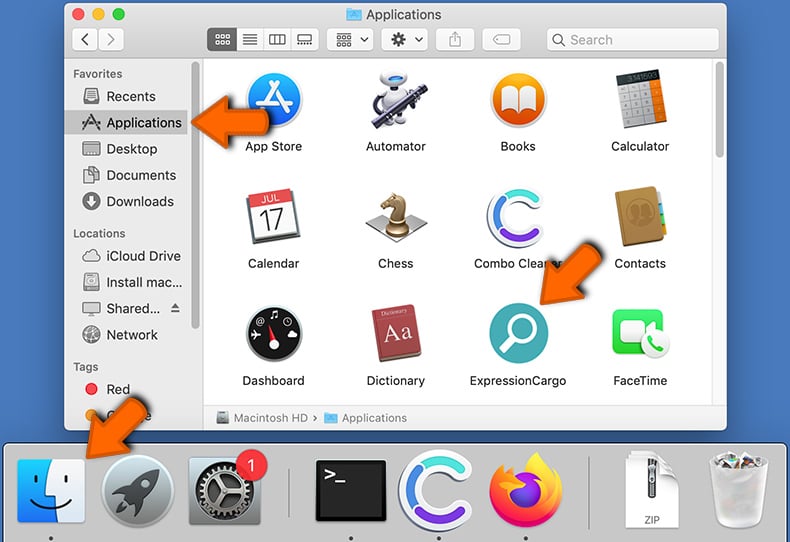
Click the Finder icon. In the Finder window, select "Applications". In the applications folder, look for "MPlayerX","NicePlayer", or other suspicious applications and drag them to the Trash. After removing the potentially unwanted application(s) that cause online ads, scan your Mac for any remaining unwanted components.
Frequently Asked Questions (FAQ)
My computer is infected with Cuckoo malware, should I format my storage device to get rid of it?
No, Cuckoo's removal does not necessitate such drastic measures.
What are the biggest issues that Cuckoo malware can cause?
The threats posed by an infection depend on the malware's functionalities and the cyber criminals' modus operandi. Cuckoo functions as spyware and a stealer, i.e., it can record and extract sensitive data. Generally, infections of this kind can lead to severe privacy issues, financial losses, and identity theft.
What is the purpose of Cuckoo malware?
Malware is most commonly used for profit. However, cyber criminals can also employ malicious software to amuse themselves, realize personal grudges, disrupt processes (e.g., websites, services, companies, etc.), and launch politically/geopolitically motivated attacks.
How did Cuckoo malware infiltrate my computer?
Cuckoo was spread through a trojanized streaming platform music converter app (e.g., "DumpMedia Spotify Music Converter"). However, this malware could be proliferated by relying on other techniques.
In general, malicious software is distributed via untrustworthy download sources (e.g., freeware and third-party sites, P2P sharing networks, etc.), pirated content, drive-by downloads, spam mail, online scams, illegal program activation ("cracking") tools, and fake updates.
Will Combo Cleaner protect me from malware?
Yes, Combo Cleaner is designed to scan devices and eliminate all kinds of threats. It is capable of removing most of the known malware infections. Note that since sophisticated malicious programs typically hide deep within systems – performing a complete system scan is paramount.

▼ Show Discussion