How to identify scams like "Hello My Perverted Friend"
![]() Written by Tomas Meskauskas on (updated)
Written by Tomas Meskauskas on (updated)
What kind of scam is "Hello My Perverted Friend"?
After careful examination, it has been determined that the content of this email corresponds to a sextortion scam. Sextortion scams involve cybercriminals threatening to reveal compromising or intimate content of the victim unless a certain amount of money is paid, exploiting fear and embarrassment for financial gain.
More about the "Hello My Perverted Friend" scam email
This is a classic sextortion scam where the sender claims to be a hacker who has allegedly gained access to the victim's device, including their browser history and webcam footage. The scammer threatens to expose compromising videos of the victim engaging in explicit activities unless a ransom of $890 in Bitcoin is paid within 48 hours.
The scammer asserts control over all the victim's devices and warns against contacting the authorities or attempting to reset the system. The victim is urged not to respond to the email and is given instructions on how to make the cryptocurrency payment.
It is important to recognize such scams as attempts to exploit fear and embarrassment for financial gain, and individuals are advised not to comply with the scammer's demands. Scammers often use false claims about having compromising information or access to personal devices to coerce victims into paying.
Also, scammers rarely have the claimed evidence, and their primary goal is to extract money from victims. Thus, recipients should not engage with or pay scammers in such situations.
| Name | Hello My Perverted Friend Email Scam |
| Threat Type | Sextortion Scam, Fraud |
| Fake Claim | Explicit material will be disclosed if a ransom is not paid |
| Cyber Criminal Cryptowallet Address | 1LbbzFmNMMFMwsketCSzxAur6yinXBSiQQ, 13BfNz9CsS9YHDs2UeDkH6m7rZDM4Xo81u, 112TaHP3wQrJ2QWXmgPt6qssFVWBqUmT5b, 1A28fiWUfQnqEMqoDmMf7KZcjSDY7mEjfs, 1FXXt4n3GnZKGJeK4LkHmZdKxwpgMwS67e |
| Ransom Amount | $890 |
| Symptoms | Unauthorized online purchases, changed online account passwords, identity theft, illegal access of the computer. |
| Distribution methods | Deceptive emails, rogue online pop-up ads, search engine poisoning techniques, misspelled domains. |
| Damage | Loss of sensitive private information, monetary loss, identity theft. |
| Malware Removal (Windows) | To eliminate possible malware infections, scan your computer with legitimate antivirus software. Our security researchers recommend using Combo Cleaner. |
Similar scam emails in general
Sextortion scams share common traits of false claims regarding compromising information, threats of unauthorized access to personal devices, and demands for cryptocurrency payments, typically in Bitcoin. These scams use fear and urgency to coerce victims into paying, often avoiding specific details and discouraging involvement of law enforcement.
Recognizing these patterns is vital for individuals to avoid falling prey to such scams and to prioritize bolstering their online security measures. It is important to note that scam emails can contain attachments or links intended to infect computers with malware.
Examples of scam emails are "LEDGER SECURITY Email Scam", "Glacier Bank Email Scam", and "Apple Security Releases Email Scam".
How do spam campaigns infect computers?
Typically, malicious actors send emails that appear genuine to deceive recipients into opening harmful links or downloading infected attachments. These attachments, often disguised as innocent documents like PDFs or Word files, carry concealed malicious payloads. When users open these attachments, the malware is triggered, compromising the security of their devices.
Additionally, clicking on malicious links may direct users to pages hosting malware or initiate drive-by downloads, exposing their systems to potential threats.
How to avoid installation of malware?
Exercise caution with unexpected or irrelevant emails from unknown addresses. Avoid opening links or attachments presented in such emails. Do not download pirated software or use P2P networks, third-party app stores, and similar sources for downloading apps or files. Download them from official sites (or app stores).
Regularly update the operating system and programs, and use reputable antivirus and anti-malware software. If you have already opened malicious attachments, we recommend running a scan with Combo Cleaner Antivirus for Windows to automatically eliminate infiltrated malware.
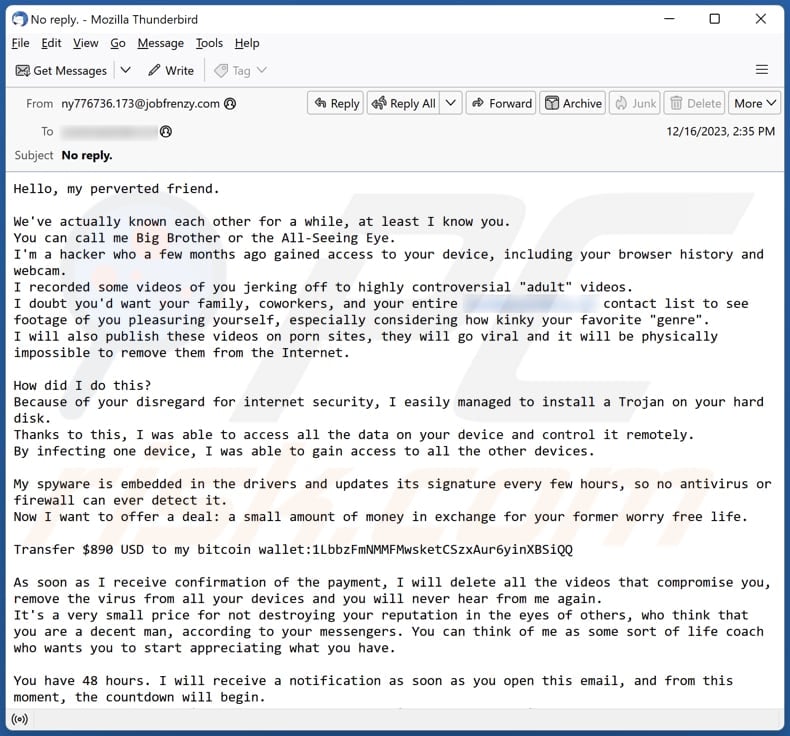
Text presented in the "Hello My Perverted Friend" email letter:
Subject: No reply.
Hello, my perverted friend.We've actually known each other for a while, at least I know you.
You can call me Big Brother or the All-Seeing Eye.
I'm a hacker who a few months ago gained access to your device, including your browser history and webcam.
I recorded some videos of you jerking off to highly controversial "adult" videos.
I doubt you'd want your family, coworkers, and your entire ******** contact list to see footage of you pleasuring yourself, especially considering how kinky your favorite "genre".
I will also publish these videos on porn sites, they will go viral and it will be physically impossible to remove them from the Internet.How did I do this?
Because of your disregard for internet security, I easily managed to install a Trojan on your hard disk.
Thanks to this, I was able to access all the data on your device and control it remotely.
By infecting one device, I was able to gain access to all the other devices.My spyware is embedded in the drivers and updates its signature every few hours, so no antivirus or firewall can ever detect it.
Now I want to offer a deal: a small amount of money in exchange for your former worry free life.Transfer $890 USD to my bitcoin wallet:1LbbzFmNMMFMwsketCSzxAur6yinXBSiQQ
As soon as I receive confirmation of the payment, I will delete all the videos that compromise you, remove the virus from all your devices and you will never hear from me again.
It's a very small price for not destroying your reputation in the eyes of others, who think that you are a decent man, according to your messengers. You can think of me as some sort of life coach who wants you to start appreciating what you have.You have 48 hours. I will receive a notification as soon as you open this email, and from this moment, the countdown will begin.
If you've never dealt with cryptocurrency before, it's very easy. Simply type "cryptocurrency exchange" into a search engine, and then all set.Here's what you shouldn't do:
- Don't reply to my email. It was sent from a temporary email account.
- Don't call the police. Remember, I have access to all your devices, and as soon as I notice such activity, it will automatically lead to the publishing of all the videos.
- Don't try to reinstall your system or reset your device. First of all, I already have the videos, and secondly, as I said, I have remote access to all your devices, and once I notice such an attempt, you know what happens.Remember, crypto addresses are anonymous, so you won't be able to track down my wallet.
So long story short, let's resolve this situation with a benefit for me and you.
I always keep my word unless someone tries to trick me.Lastly, a little advice for the future. Start taking your online security more seriously.
Change your passwords regularly and set up multi-factor authentication on all your accounts.Best wishes.
Full appearance of "Hello My Perverted Friend" scam email:
Another example of an email from "Hello My Perverted Friend" spam campaign:
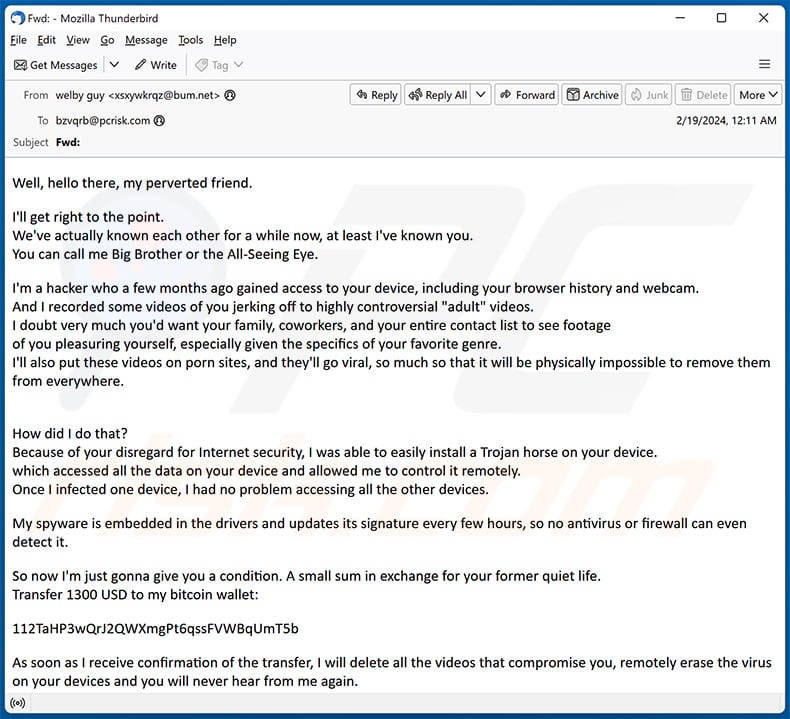
Text presented within:
Subject: Fwd:
Well, hello there, my perverted friend.I'll get right to the point.
We've actually known each other for a while now, at least I've known you.
You can call me Big Brother or the All-Seeing Eye.I'm a hacker who a few months ago gained access to your device, including your browser history and webcam.
And I recorded some videos of you jerking off to highly controversial "adult" videos.
I doubt very much you'd want your family, coworkers, and your entire contact list to see footage
of you pleasuring yourself, especially given the specifics of your favorite genre.
I'll also put these videos on porn sites, and they'll go viral, so much so that it will be physically impossible to remove them from everywhere.
How did I do that?
Because of your disregard for Internet security, I was able to easily install a Trojan horse on your device.
which accessed all the data on your device and allowed me to control it remotely.
Once I infected one device, I had no problem accessing all the other devices.My spyware is embedded in the drivers and updates its signature every few hours, so no antivirus or firewall can even detect it.
So now I'm just gonna give you a condition. A small sum in exchange for your former quiet life.
Transfer 1300 USD to my bitcoin wallet:112TaHP3wQrJ2QWXmgPt6qssFVWBqUmT5b
As soon as I receive confirmation of the transfer, I will delete all the videos that compromise you, remotely erase the virus on your devices and you will never hear from me again.
Agree, it's a very small price to pay for not destroying your reputation in the eyes of others who, judging by your correspondence in messengers,
has an opinion of you as a decent human being.
You can think of me as a kind of mentor who wants you to start appreciating what you have.You have 48 hours - I'll be notified as soon as you open this letter, and from then on it's a countdown.
If you've never dealt with cryptocurrency before, it's super easy - type "crypto exchange" into a search engine, and the next thing to do.Here's what you shouldn't do:
Don't reply to my email. It was sent from a disposable e-mail account.
Don't call law enforcement. Remember, I have access to all of your devices, and as soon as I notice such activity, it will automatically lead to the release of all of your data.
Do not attempt to reinstall your system or factory reset your device.
First of all, I already have the video and all your data, and secondly, as I already said, I have remote access to all your devices and as soon as I notice such an attempt, it will lead to irreversible consequences.
Remember that crypto-addresses are anonymous, so you won't be able to figure me out from my wallet.
Anyway, let's make this a win-win situation.
I always keep my word, unless I'm being tricked.
Advice for the future: take more seriously your security on the Internet. Also regularly change passwords and set up multi-factor authorization on all your accounts.
Instant automatic malware removal:
Manual threat removal might be a lengthy and complicated process that requires advanced IT skills. Combo Cleaner is a professional automatic malware removal tool that is recommended to get rid of malware. Download it by clicking the button below:
▼ DOWNLOAD Combo Cleaner
By downloading any software listed on this website you agree to our Privacy Policy and Terms of Use. To use full-featured product, you have to purchase a license for Combo Cleaner. 7 days free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Quick menu:
- What is Hello My Perverted Friend sextortion scam?
- Types of malicious emails.
- How to spot a malicious email?
- What to do if you fell for an email scam?
Types of malicious emails:
![]() Phishing Emails
Phishing Emails
Most commonly, cybercriminals use deceptive emails to trick Internet users into giving away their sensitive private information, for example, login information for various online services, email accounts, or online banking information.
Such attacks are called phishing. In a phishing attack, cybercriminals usually send an email message with some popular service logo (for example, Microsoft, DHL, Amazon, Netflix), create urgency (wrong shipping address, expired password, etc.), and place a link which they hope their potential victims will click on.
After clicking the link presented in such email message, victims are redirected to a fake website that looks identical or extremely similar to the original one. Victims are then asked to enter their password, credit card details, or some other information that gets stolen by cybercriminals.
![]() Emails with Malicious Attachments
Emails with Malicious Attachments
Another popular attack vector is email spam with malicious attachments that infect users' computers with malware. Malicious attachments usually carry trojans that are capable of stealing passwords, banking information, and other sensitive information.
In such attacks, cybercriminals' main goal is to trick their potential victims into opening an infected email attachment. To achieve this goal, email messages usually talk about recently received invoices, faxes, or voice messages.
If a potential victim falls for the lure and opens the attachment, their computers get infected, and cybercriminals can collect a lot of sensitive information.
While it's a more complicated method to steal personal information (spam filters and antivirus programs usually detect such attempts), if successful, cybercriminals can get a much wider array of data and can collect information for a long period of time.
![]() Sextortion Emails
Sextortion Emails
This is a type of phishing. In this case, users receive an email claiming that a cybercriminal could access the webcam of the potential victim and has a video recording of one's masturbation.
To get rid of the video, victims are asked to pay a ransom (usually using Bitcoin or another cryptocurrency). Nevertheless, all of these claims are false - users who receive such emails should ignore and delete them.
How to spot a malicious email?
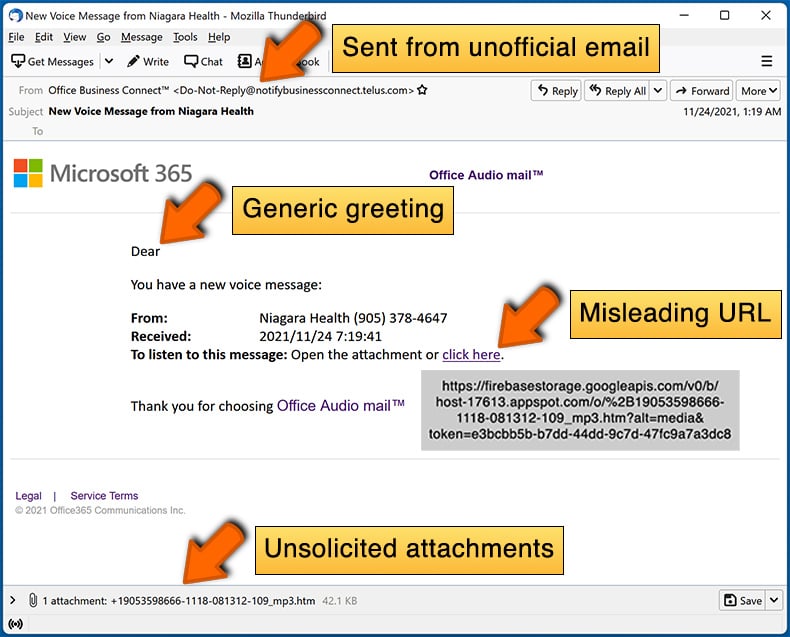
While cyber criminals try to make their lure emails look trustworthy, here are some things that you should look for when trying to spot a phishing email:
- Check the sender's ("from") email address: Hover your mouse over the "from" address and check if it's legitimate. For example, if you received an email from Microsoft, be sure to check if the email address is @microsoft.com and not something suspicious like @m1crosoft.com, @microsfot.com, @account-security-noreply.com, etc.
- Check for generic greetings: If the greeting in the email is "Dear user", "Dear @youremail.com", "Dear valued customer", this should raise suspiciousness. Most commonly, companies call you by your name. Lack of this information could signal a phishing attempt.
- Check the links in the email: Hover your mouse over the link presented in the email, if the link that appears seems suspicious, don't click it. For example, if you received an email from Microsoft and the link in the email shows that it will go to firebasestorage.googleapis.com/v0... you shouldn't trust it. It's best not to click any links in the emails but to visit the company website that sent you the email in the first place.
- Don't blindly trust email attachments: Most commonly, legitimate companies will ask you to log in to their website and to view any documents there; if you received an email with an attachment, it's a good idea to scan it with an antivirus application. Infected email attachments are a common attack vector used by cybercriminals.
To minimise the risk of opening phishing and malicious emails we recommend using Combo Cleaner Antivirus for Windows.
Example of a spam email:
What to do if you fell for an email scam?
- If you clicked on a link in a phishing email and entered your password - be sure to change your password as soon as possible. Usually, cybercriminals collect stolen credentials and then sell them to other groups that use them for malicious purposes. If you change your password in a timely manner, there's a chance that criminals won't have enough time to do any damage.
- If you entered your credit card information - contact your bank as soon as possible and explain the situation. There's a good chance that you will need to cancel your compromised credit card and get a new one.
- If you see any signs of identity theft - you should immediately contact the Federal Trade Commission. This institution will collect information about your situation and create a personal recovery plan.
- If you opened a malicious attachment - your computer is probably infected, you should scan it with a reputable antivirus application. For this purpose, we recommend using Combo Cleaner Antivirus for Windows.
- Help other Internet users - report phishing emails to Anti-Phishing Working Group, FBI’s Internet Crime Complaint Center, National Fraud Information Center and U.S. Department of Justice.
Frequently Asked Questions (FAQ)
Why did I receive this email?
This email is generic, sent to many recipients, and is part of a mass email campaign. These campaigns often target a broad audience with the hope that some recipients will fall for scams.
I have provided my personal information when tricked by this email, what should I do?
If you have shared any account credentials, promptly update all passwords. If you have disclosed other personal information, such as credit card details, social security numbers, or ID card information, reach out to the relevant authorities.
I have downloaded and opened a malicious file attached to an email, is my computer infected?
It depends on the file type. For instance, if the file was an executable (.exe), there is a high likelihood of infection. Conversely, if it was a document file (.pdf, .doc, or similar), you might have avoided the risk, as merely opening such documents does not always lead to a system compromise.
Was my computer actually hacked and does the sender have any information?
No, your computer has not been genuinely hacked or infected. Scammers may have acquired old passwords obtained from databases that contain compromised information.
I have sent cryptocurrency to the address presented in such email, can I get my money back?
Crypto transactions are untraceable, making it impossible to recover the funds.
I have read the email but did not open the attachment, is my computer infected?
Merely opening an email is entirely harmless. The risk arises when recipients open links or attached files, as these actions can lead to system infections.
Will Combo Cleaner remove malware infections that were present in email attachment?
Combo Cleaner can identify and eradicate nearly all recognized malware infections. It is essential to acknowledge that advanced malware often hides extensively within the system. As a result, performing a thorough full system scan is a necessity.
▼ Show Discussion